CISA provides details of Federal Agency Network attack through GeoServer vulnerability
Take action: This is one of those very scary stories, where there were multiple chances to prevent or detect the attack earlier, but the attack still continued. Any organization security is far from perfect. All we can share is the lessons learned and advise a bit more discipline, first with fast patching.
Learn More
CISA has published an analysis of a cyberattack that successfully breached an unnamed U.S. federal civilian executive branch (FCEB) agency by exploiting of a critical vulnerability in GeoServer software. This incident remained undetected for three weeks.
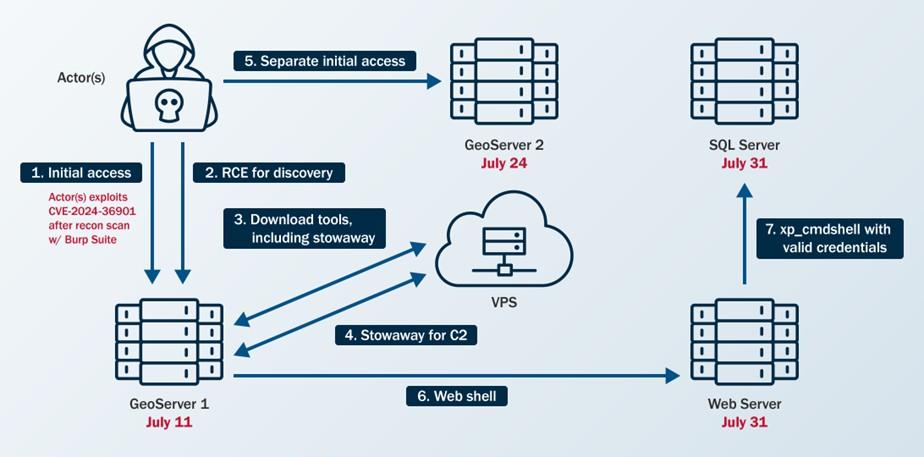
Overview of Threat Actor Activity. Source: CISA
- Hackers first gained access to the federal agency's network on July 11, 2024, by exploiting CVE-2024-36401 on a public-facing GeoServer instance.
- The vulnerability had been publicly disclosed on June 30, 2024, just eleven days before its exploitation, with patches becoming available on June 18, 2024. Despite the severity of the flaw and its rapid public disclosure, the agency failed to implement timely remediation measures.
- The attackers exploited the same vulnerability on a second GeoServer instance on July 24, 2024, shortly after CISA had added CVE-2024-36401 to its Known Exploited Vulnerabilities (KEV) catalog on July 15, 2024.
- Initial reconnaissance was conducted using Burp Suite Burp Scanner to identify vulnerable GeoServer instances within the agency's infrastructure. After exploitation, the attackers downloaded various open-source tools and scripts to establish persistence and perform lateral movement through the network.
- Attackers moved laterally from the initial GeoServer to a web server and subsequently to an SQL server. They deployed multiple tools and techniques:
- China Chopper web shell, a lightweight tool commonly used by Chinese threat actors for maintaining remote access and control.
- The attackers also created cron jobs for scheduled command execution, attempted privilege escalation using the publicly available DirtyCow exploit targeting CVE-2016-5195, and deployed the RingQ defense evasion tool.
- For command and control communications, they utilized the Stowaway multi-level proxy tool to establish outbound connections over TCP ports 4441 and 50012, effectively bypassing network security restrictions and maintaining covert access to internal resources.
The incident remained undetected for three weeks, exposing critical gaps in the agency's security monitoring capabilities. Detection finally occurred on July 31, 2024, when the agency's Endpoint Detection and Response (EDR) tool flagged a suspicious file named "1.txt" as suspected malware on the SQL server.
The EDR system had generated an earlier alert on July 15, 2024, when it detected the Stowaway tool on the first GeoServer, but this alert was not reviewed by the Security Operations Center (SOC)
The specific types and volume of data accessed or stolen have not been disclosed by CISA. The number of affected individuals remains undisclosed, though the incident impacted an entire federal agency's network infrastructure.
CISA's investigation revealed several security deficiencies within the affected agency.
- The agency's Web Server completely lacked endpoint protection,
- The incident response plan had not been properly tested or exercised, nor did it include procedures for engaging third parties and providing them with necessary access to security tools.
- When CISA personnel were brought in to assist with the incident response, the agency could not grant them remote access to the Security Information and Event Management (SIEM) system, hampering the investigation's speed and efficiency.
The advisory emphasizes three critical lessons learned from this incident.
- Vulnerabilities were not promptly remediated despite public disclosure and inclusion in CISA's KEV catalog. While July 24, 2024, technically fell within the KEV-required patching window, CISA stressed that organizations should address known exploited vulnerabilities immediately rather than waiting for mandated deadlines.
- The agency's incident response plan lacked adequate procedures for engaging third-party assistance and granting necessary access to security tools, creating substantial delays in containment and remediation efforts.
- EDR alerts were not continuously monitored across all systems, allowing critical security events to go unnoticed for extended periods.
