Security and Architecture
Here at BeyondMachines security of our processes and implementation it is essential because our users trust us to deliver cybersecurity knowledge, awareness and good practices. We can't do that unless we practice what we preach.
We are constantly developing our security infrastructure and processes to ensure the safeguarding of our customer’s data.
Our guiding principles of Information Security are:
- ISO7001:2013 - which we practice in our processes and technical protections
- DIE model - distributed, immutable and ephemeral which we practice in our implmenetation and architecture
We are transparent about our architectural concept and data flows, which are part of this page.
Organizational practices
We implement ongoing, relevant, and up-to-date security pracitces with all of our team members.
- All access to data is based on need-to-know and need-to-access segregation of duties within the team.
- We consider all user data as confidential and we don't share them with the public;
- Direct access to server systems is restricted - all changes are performed as infrastructure as a code, all database changes are performed via migrations which are peer-reviewed before deploying.
- Every team member is identified with their own credentials, and we don't use shared credentials.
- We use MFA and SSO on every tool that we use that has support for SSO or MFA
- Our endpoints are encrypted at rest and password protected, including screen saver passwords.
- We update our endpoints as soon as patches are available;
- We use only licensed or open source tools;
- We use antimalware products on on all our endpoints.
- We perform mutual awareness and knowledge improvement sessions through the building of our product.
- User is not stored on endpoints.
Technical practices
We implement sound technical practices and protections of our platform
- Data location in advanced datacenters - The BeyondMachines platform is hosted in AWS eu-central-1region datacenters, which take on the responsibilities of datacenter physical, environmental and network protection.
- High availability by design - The BeyondMachines platform is designed to run in multiple availability zones, thus surviving an incident that will fail an entire datacenter.
- Data encryption in transit and at rest - All internal service communications and communications between our service and Slack are encrypted via TLS. Sensitive data such as standup reports are encrypted at rest using AES256.
- Backups of data are protected - all backups of data are stored encrypted at rest and stored only in a datacenter setting - not on endpoints or external storage.
- Data retention - We store all user data only while it's needed, and delete it after the fact. All logs are stored for a maximum of 6 months and are automatically deleted after that.
- Incident management - Our company continuously monitors for adverse events and we will inform you in the event of any security breach or unauthorized access to your data.
- Proper technical authentication - our external integrations are done via OAuth 2, which enables the user to clearly understand and control which access our platform gets to their data.
- Source code review - all source code is peer-reviewed before being accepted to be merged to the main branch for production.
- Source code vulnerability scans - all source code is passed through two source code vulnerability scanners and two linters for code quality.
- Third party source code vulnerability monitoring - all third party libraries are monitored for vulnerabilities using Depedabot and are patched upon detection of vulnerability.
- All secrets are kept in secure storage on AWS
- Automated deployment - all deployment of source code is automated and doesn't require administrator actions on server systems
- Penetration tests - the platform passes an annual penetration test by external testers.
Architecture diagrams and data flows
Architecture of the BeyondMachines platform

Data flow of the BeyondMachines App Slack Installation

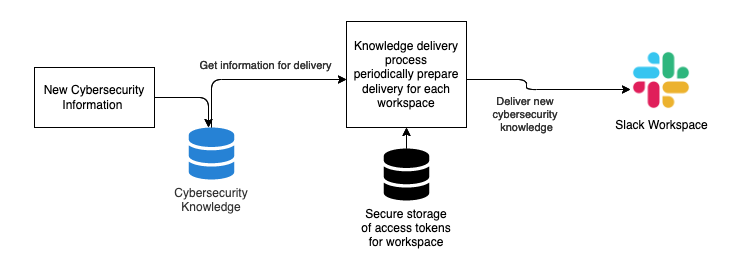
Data flow of the BeyondMachines knowledge communication
Contact us
If you have any questions, comments, or concerns, you may contact us at contact [at] beyondmachines [dot] net.
Change log
- 08 May 2022: Initial version