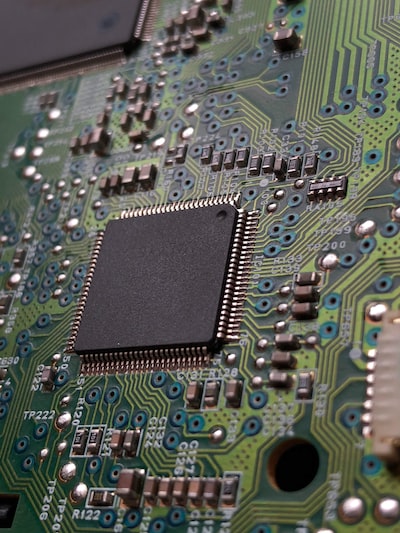
Zenbleed critical flaw reported in AMD Ryzen 2 and EPYC CPUs
Take action: A complex patch to a risk that most users will try to push back against: The patching of microcode is a hassle and the entire exploit scenario requires that a malicious program is present on the system. But nobody can be sure that a malicious program won't be brought - especially to a server system Virtual Machine. Plan for patching, prioritize server systems running AMD CPUs. Then put pressure on the end users.
Learn More
A critical vulnerability, CVE-2023-20593 (aka "zenbleed") has been identified in several AMD processors, including Ryzen and EPYC series.
The following processors are impacted:
- AMD Ryzen 3000 Series Processors
- AMD Ryzen PRO 3000 Series Processors
- AMD Ryzen Threadripper 3000 Series Processors
- AMD Ryzen 4000 Series Processors with Radeon Graphics
- AMD Ryzen PRO 4000 Series Processors
- AMD Ryzen 5000 Series Processors with Radeon Graphics
- AMD Ryzen 7020 Series Processors with Radeon Graphics
- AMD EPYC 7002 Series Processors
This flaw stems from the vector register file (RF) that's shared among all tasks on the same physical core of a CPU. The vulnerability arises a flag is set speculatively and remains unset upon branch misprediction, potentially leading to a use-after-free (UaF) scenario.Under specific conditions involving merge optimization, register rename, and mispredicted instruction, this UaF scenario can occur.
The practical implication of this security loophole is that attackers can spy on the registers of other processes without requiring any system calls or special privileges. This vulnerability traverses all isolation including machine sandbox and affects various operating systems.
AMD has released a patch for the vulnerability.
For organizations and users who can't apply the patch, an alternative software workaround involves setting the "chicken bit" DE_CFG[9].
For Linux users, msr-tools can be used to set the chicken bit on all cores with a specific command (# wrmsr -a 0xc0011029 $(($(rdmsr -c 0xc0011029) | (1<<9)))). FreeBSD users can employ cpucontrol(8). For other operating systems, the vendors should provide workaround options.
Applying the microcode update is the preferred solution to the workaround. It's important to note that disabling SMT (Simultaneous Multi-Threading) is not sufficient to mitigate this vulnerability.