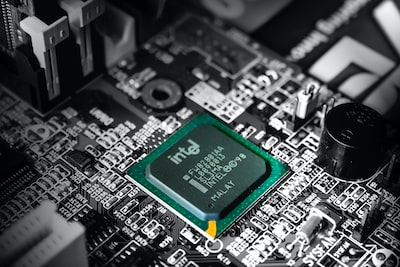
Intel Patches vulnerability found in many generations of Processors
Take action: Similar to the Inception attack on AMD processors, this vulnerability requires that you load malware in memory. It won't happen tomorrow but it will happen eventually. You can always accept the risk and carry on with a little more CPU speed and a little more exposure. Just remember that security failures are not one specific big problem. It's always a combination of all the little risks you accepted.
Learn More
Intel has successfully addressed the security vulnerability known as "Downfall," a term coined by the researcher who discovered it, Daniel Moghimi from the University of California San Diego.
This critical weakness impacts a vast number of modern processors, with the vulnerability affecting Intel processors released between 2015 and 2019. Specifically, processors from the 6th-gen Skylake to the 11th-gen Tiger Lake are susceptible to the vulnerability. Intel has released a comprehensive list detailing the specific chips affected. Interestingly, Intel has chosen to refer to the vulnerability as "Gather Data Sampling" (GDS) instead of "Downfall."
The vulnerability, tracked as CVE-2022-40982, enables hackers to target valuable credentials like passwords and encryption keys. The unique characteristic of this vulnerability is that the attacker and victim need to share the same physical CPU core, a seemingly improbable scenario. However, considering the prevalence of multitasking, multithreading, and the nature of servers and cloud computing, Moghimi suggests that this flaw "most likely" has broad implications for a wide range of users.
The positive news is that Intel has taken swift action to release a solution for the vulnerability. However, there is a downside: the fix does come at a cost of significant performance reduction for specific workload types. Intel anticipates that scientific and visualization engineering workloads will bear the brunt of this performance impact. Moghimi suggests that the mitigation's overhead could be substantial, potentially reaching up to 50% depending on the specific workload.
Intel recommends that users of affected Intel® Processors update to the latest version firmware provided by the system manufacturer that addresses these issues.
In response to these challenges, Intel has opted to implement the mitigation by default while offering an opt-out mechanism for those who prefer to disable it. Although this opt-out approach provides flexibility, it also introduces uncertainty. As a result, the extent to which Intel servers are immune to the vulnerability remains uncertain, as the decision to apply the fix ultimately rests with the server owner.