Most Windows and Linux computers vulnerable to a new cyberattack
Take action: Keep up with the UEFI/Firmware updates for your computer, since the patch needs to be applied to the UEFI part of the computer. It's not a trivial process, proper reading of instructions is needed and one or more reboots. But since the vulnerability exists below the level of the operating system nothing else protects you. In the meantime, keep your device physically secure and be very careful with running programs and opening emails.
Learn More
A new cybersecurity threat, dubbed LogoFAIL, has been identified to pose a significant risk to most Windows and Linux-powered devices. Researchers from Binarly who discovered the vulnerability believe it affects almost every device running these operating systems.
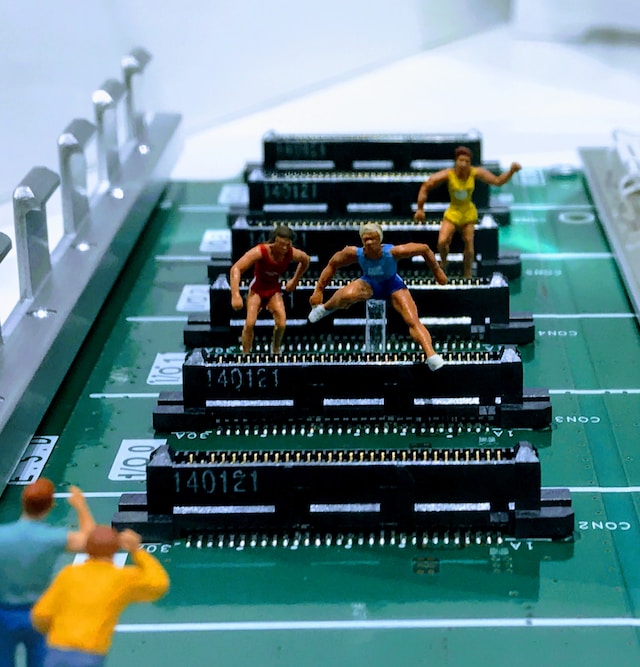
LogoFAIL enables attackers to execute harmful code on devices in a manner that renders most antivirus or endpoint protection tools ineffective. The vulnerability is linked to the Unified Extensible Firmware Interface (UEFI), which is running during device boot-up. While the UEFI is running the manufacturer's logo is displayed on the screen. Researchers assert that UEFI has been susceptible to approximately two dozen flaws, which could be chained to substitute the boot-up logo image with one containing malicious code. Because there is no antimalware running in that phase of the startup, such an attack is undetected by standard security measures.
LogoFAIL affects a broad spectrum of devices, encompassing the entire x64 and ARM CPU ecosystems, including UEFI suppliers like AMI, Insyde, and Phoenix, and device manufacturers such as Lenovo, Dell, and HP, along with CPU devices from Intel and AMD.
Patches have been released, but they vary depending on the manufacturer. Users are encouraged to review specific advisories for their devices to address the vulnerability and to update to the latest version of UEFI/Firmware.
One saving grace is that in order to execute this attack, threat actors must have physical access to the device or must compel the user to execute a program on the attacker's behalf. While physical access is more difficult to pull off, phishing and social engineering are a great way to get a user to execute a program for the attacker.
This vulnerability is tracked under multiple CVE identifiers: CVE-2023-5058, CVE-2023-39538, CVE-2023-39539, and CVE-2023-40238. This discovery underscores the importance of regular system updates and vigilant cybersecurity practices.