Moxa reports critical flaw affecting EDS-508A Ethernet switches
Take action: If you are using Moxa EDS-508A switches, make sure they are isolated from the internet and accessible only from trusted networks. Then implement the patch. The exploit vector is not immediately clear, so hackers will need some time to start attacking. But you better patch, because hackers will learn.
Learn More
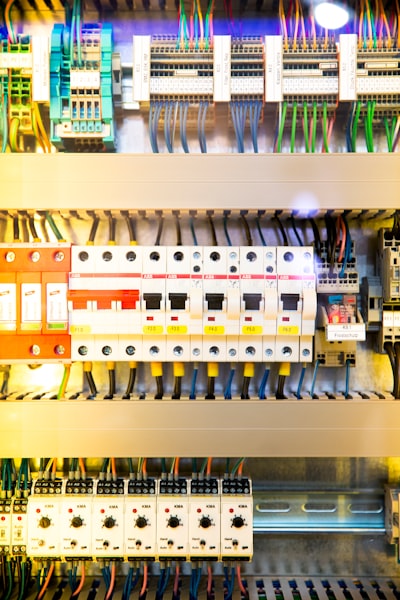
Moxa is reporting a critical security vulnerability affecting their EDS-508A Series Ethernet switches that could allow unauthorized access through authentication bypass.
The vulnerability is tracked as CVE-2024-12297 (CVSS score 9.2) and enables unauthenticated remote exploitation, requiring no user interaction and no privileges for an attacker to exploit. The security flaw could allow malicious actors to bypass authentication mechanisms, perform brute-force attacks, execute MD5 collision attacks, gain unauthorized access to sensitive configurations, and potentially disrupt services.
The affected products include Moxa EDS-508A Series Ethernet switches running firmware version 3.11 and earlier.
Moxa has released a security patch that is available through their Technical Support team.
Organizations using these devices are strongly advised to implement several recommended mitigations, including minimizing network exposure by isolating devices from the Internet, implementing firewall rules to limit SSH access to trusted IP addresses, and deploying IDS/IPS systems to detect and prevent exploitation attempts.
Moxa has not disclosed whether there have been any active exploitation attempts in the wild, nor provided indicators of compromise for potentially affected systems.