Rockwell Automation fixes two vulnerabilities FactoryTalk ThinManager, one critical
Take action: If you are using Rockwell Automation FactoryTalk, make sure it's not accessible from the internet and isolating TCP 2031 only to trusted networks. Patching may be tedious, but the unauthenticated critical function merits analysis and if possible patching.
Learn More
Rockwell Automation has addressed two vulnerabilities in its FactoryTalk ThinManager product.
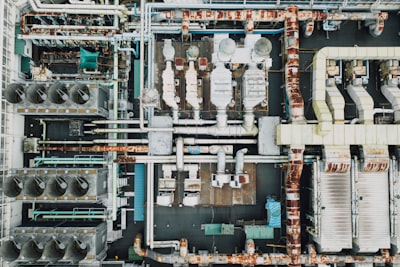
FactoryTalk ThinManager is used for managing industrial control systems in critical manufacturing sectors.
Vulnerability Summary
- CVE-2024-10386 (CVSS score 9.8) - Missing Authentication for Critical Function - allows attackers with network access to bypass authentication, potentially manipulating the device’s database. The vulnerability could be exploited remotely with low attack complexity, presenting a severe risk to critical infrastructure.
- CVE-2024-10387 (CVSS score 8.7) - Out-of-Bounds Read - could enable attackers to induce a DoS by sending crafted messages. This issue can also be exploited remotely and has a high potential to impact system availability.
Affected Versions are ThinManager: Versions 11.2.0 through 14.0.0.
Rockwell Automation has released patches on the FactoryTalk ThinManager download site. Additional mitigations include:
- Restrict TCP 2031 communication to essential devices only.
- Control systems should be behind firewalls, isolated from business networks.
- Use VPNs for secure remote access but ensure they are up-to-date to mitigate VPN-related vulnerabilities.