LockBit ransomware gang dark web site hacked, exposing crypto wallets, passwords, victim negotiations and affiliate data
Take action: Just like Everest ransomware gang and their WordPress, this is one more reason to patch your PHP. Especially if you are doing bad things, a lot of people would try to return the favor.
Learn More
The LockBit ransomware gang has experienced a significant security breach where their dark web affiliate panels were defaced and replaced with an anti-crime message. The hackers behind this breach published a MySQL database dump containing sensitive operational information, including thousands of victim negotiations and affiliate details.
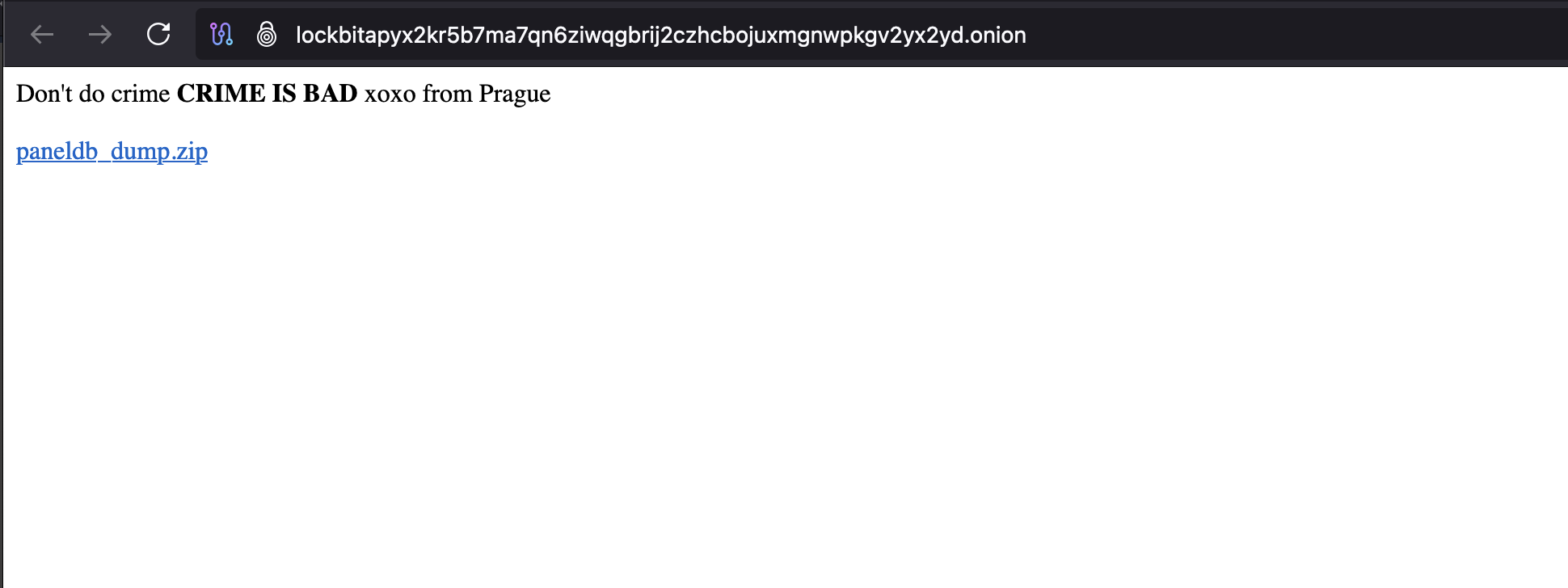
The breach was first spotted by a threat actor known as Rey, who noticed that all of LockBit's administrator panels had been defaced with the message "Don't do crime CRIME IS BAD xoxo from Prague," along with a link to download a "paneldb_dump.zip" file. This archive contained a SQL file dumped from the ransomware operation's MySQL database that powered their affiliate panel.
LockBit's operator, known as 'LockBitSupp,' has confirmed the breach in a Tox conversation with Rey, but claimed that no private keys were leaked or data lost. Based on timestamps in the database dump and the negotiation records, the breach appears to have occurred on April 29th, 2025.
While the full impact remains to be seen, this breach represents a significant exposure of LockBit's internal operations and communications with victims.
The leaked MySQL database contained multiple tables with sensitive information, including:
- 59,975 unique Bitcoin addresses used by the operation
- Details of ransomware builds created by affiliates, including some targeted company names
- Configuration files showing which ESXi servers to skip or which files to encrypt during attacks
- 4,442 negotiation messages between the ransomware operators and their victims from December 19th to April 29th
- Account details for 75 administrators and affiliates with access to the panel, including plaintext passwords
The plaintext passwords stored in LockBit's database showed poor security practices, with examples including "Weekendlover69," "MovingBricks69420," and "Lockbitproud231," as noted by security researcher Michael Gillespie.
The breach may have been facilitated by a critical vulnerability in PHP 8.1.2 (the version running on LockBit's server), tracked as CVE-2024-4577, which allows for remote code execution.
While it remains unclear who carried out the breach. The technical evidence suggests it may be the same actor or group that recently targeted the Everest ransomware operation.
Qualys Threat Research Unit extracted a list of 20 major CVEs that LockBit frequently exploited in their attacks:
- Citrix: CVE-2023-4966 (NetScaler ADC/Gateway) and CVE-2019-19781
- PaperCut: CVE-2023-27351 and CVE-2023-27350 (MF/NG)
- Microsoft: CVE-2022-21999 (Print Spooler), CVE-2021-36942 (Windows LSA), CVE-2021-34523/34473/31207 (Exchange Server), CVE-2020-1472 (Netlogon), CVE-2019-0708 (Remote Desktop Services)
- VMware: CVE-2022-22965 (Spring Framework)
- Apache: CVE-2021-44228 (Log4j2)
- F5 Networks: CVE-2021-22986 (BIG-IP)
- SonicWall: CVE-2021-20028 (SMA Firmware) and CVE-2019-7481 (SMA100)
- Fortinet: CVE-2018-13379 (FortiOS SSL VPN)
- Ivanti: CVE-2019-11510 (Pulse Connect Secure)
- Fortra: CVE-2023-0669 (GoAnywhere MFT)
- Potix: CVE-2022-36537 (ZK Framework)
