iClicker website compromised with fake ClickFix CAPTCHA installing malware
Take action: If you have ever fell for the fake CAPTCHA (press (Win + R), then (Ctrl + V), then Enter) consider your computer compromised. Reinstall it from scratch and reset ALL passwords from another secure and trusted computer.
Learn More
The website of iClicker, a popular student engagement platform and subsidiary of Macmillan, was compromised with a ClickFix social engineering attack between April 12 and April 16, 2025. iClicker's user base includes approximately 5,000 instructors and 7 million students at colleges and universities across the United States, including prominent institutions such as the University of Michigan, the University of Florida, and various universities in California.
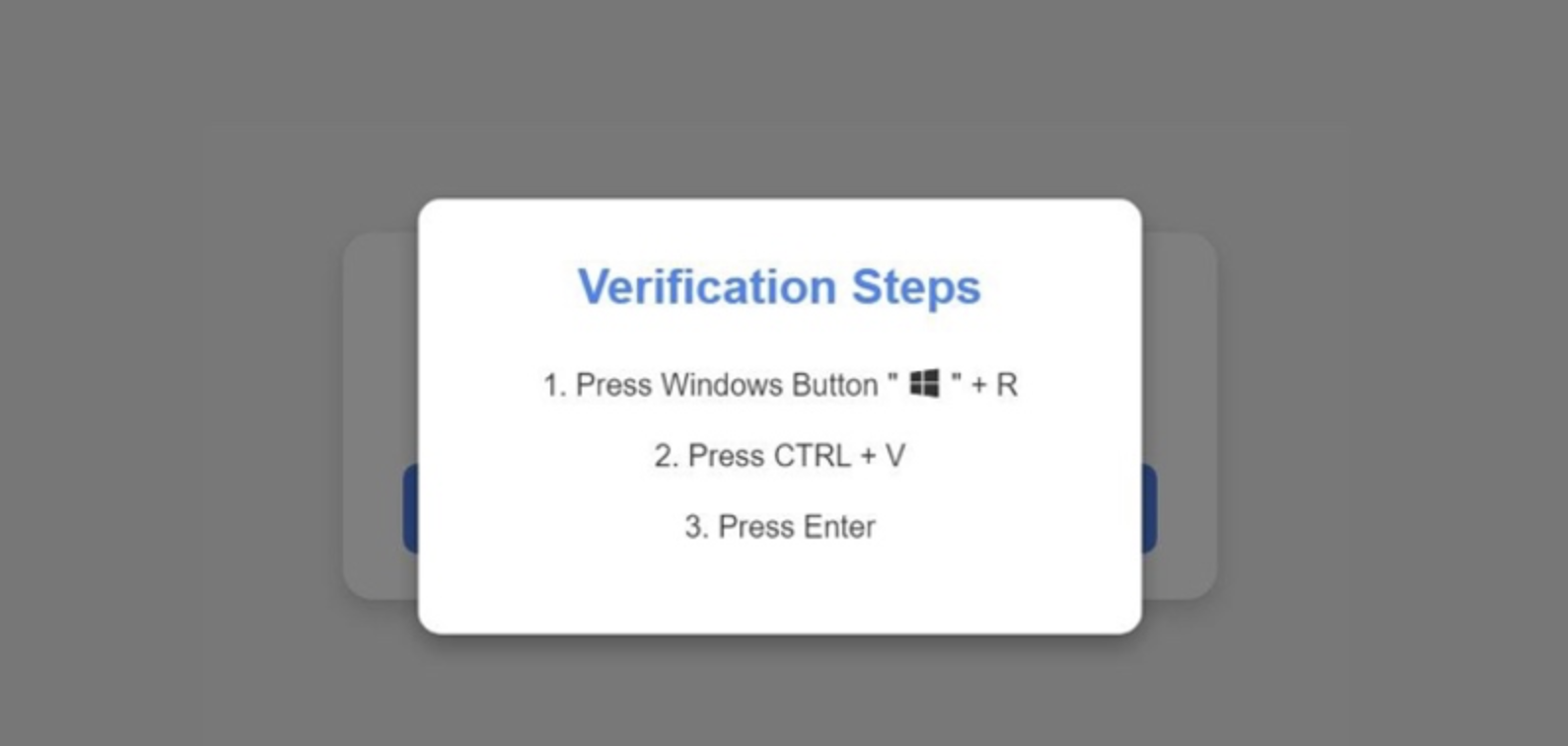
The attack used social engineering technique that displayed a fake CAPTCHA verification prompt. When visitors clicked on the "I'm not a robot" button, a PowerShell script was silently copied into the Windows clipboard. Users were then instructed to open the Windows Run dialog (Win + R), paste the PowerShell script (Ctrl + V), and execute it by pressing Enter, ostensibly to verify themselves.
The attack tricked students and instructors into installing malware on their devices.
The PowerShell command deployed in this attack was heavily obfuscated to avoid detection. When executed, it would connect to a remote server at http://67.217.228[.]14:8080 to retrieve and execute an additional PowerShell script. The specific malware ultimately installed varied depending on the type of visitor:
- For targeted victims, the script would download malware providing the threat actor with full access to the infected device.
- For non-targeted visitors or malware analysis systems, the script would instead download and run a legitimate Microsoft Visual C++ Redistributable to avoid detection.
The exact malware payload wasn't definitively identified, based on similar ClickFix campaigns, it likely deployed an information stealer designed to exfiltrate sensitive data from infected systems. The potential data compromised from affected devices could include:
- Cookies
- Login credentials
- Passwords
- Credit card information
- Browsing history
- Cryptocurrency wallets
- Private keys
- Sensitive text files (including seed.txt, pass.txt, ledger.txt, and others)
The stolen information could be used for further attacks, sold on cybercrime marketplaces, or leveraged to conduct widescale breaches potentially leading to ransomware attacks. Given the academic target audience, the attackers may have specifically sought credentials to facilitate attacks on college networks.
iClicker published a security bulletin on May 6, 2025, confirming the incident but emphasizing that no iClicker data, apps, or operations were directly impacted, and the identified vulnerability on the landing page has been resolved.
The number of affected individuals was not disclosed. No information was shared about how the attackers initially compromised the iClicker website, but it appears to be a software vulnerability.
