Complex phishing campaign impersonating Macedonian Post, stealing personal and card data
Take action: Never trust unexpected messages, and DON'T RUSH. Nothing is too urgent. Don't click on links, respond or call numbers in unexpected messages. Instead, call or visit the official website/phone of the claimed institution (manually entered site or phone number).
Learn More
A phishing campaign is currently targeting users by impersonating the North Macedonia Postal Service ("Пошта на Северна Македонија").
This is an extensive campaign, probably auto-sending to sequential numbers since we got reports from at least 4 different people and at least one of them has a brand new phone number - in use only four days!
As of 23rd of May the scam continues with a new domain link ostlmks.cfd!
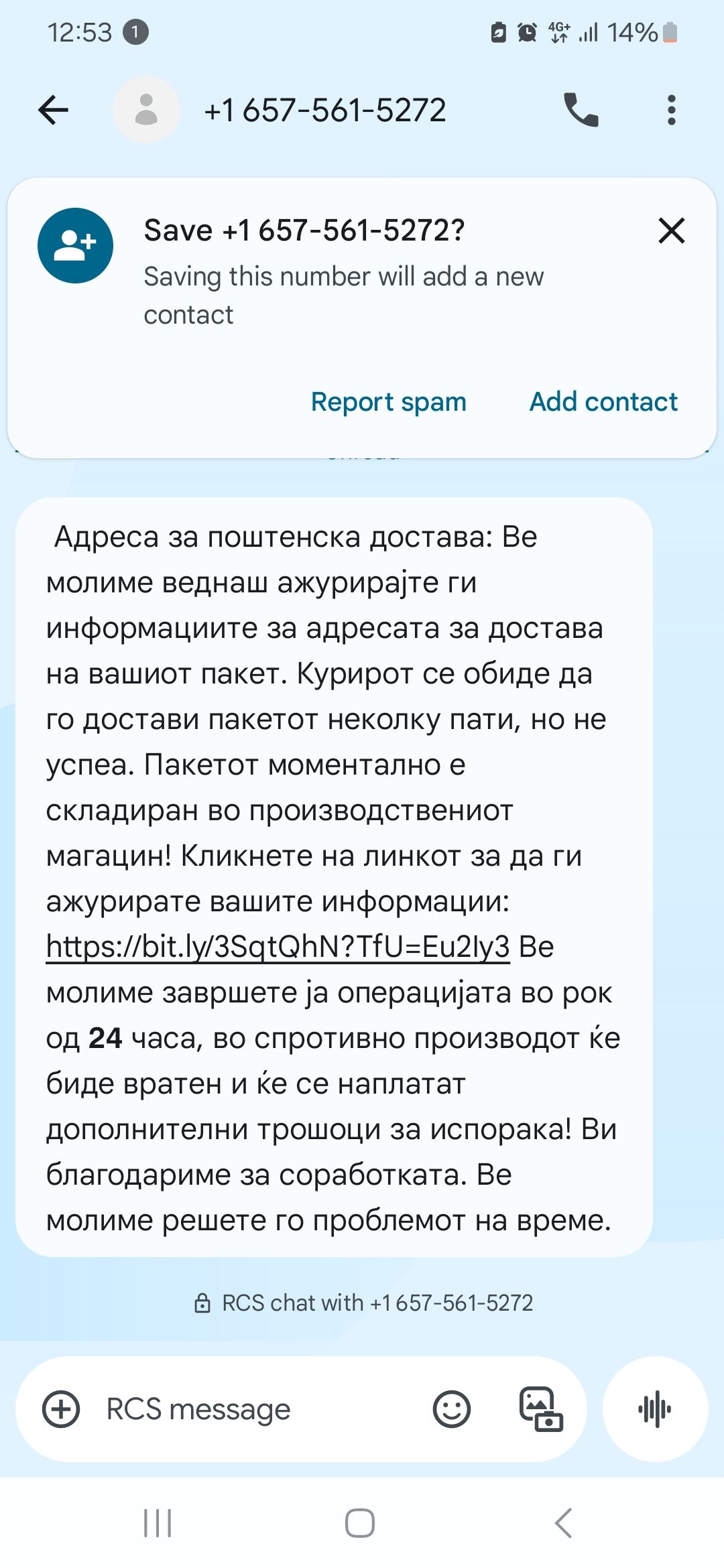
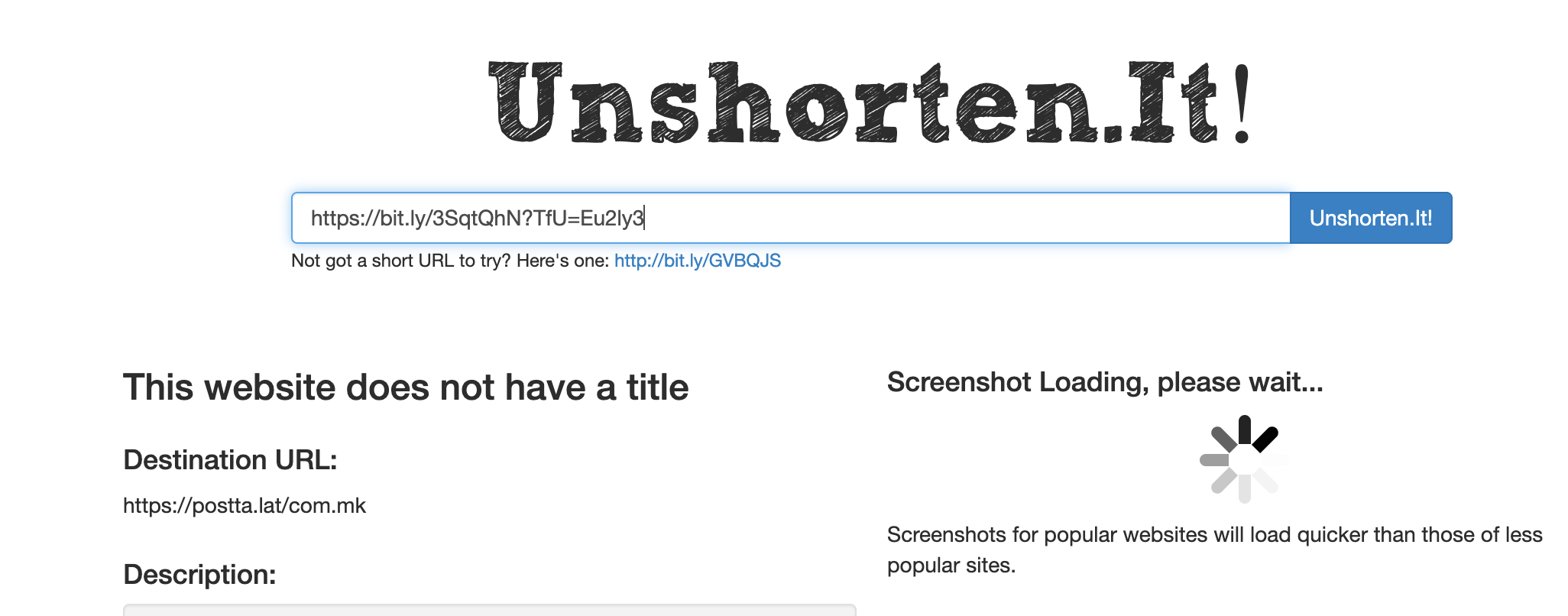
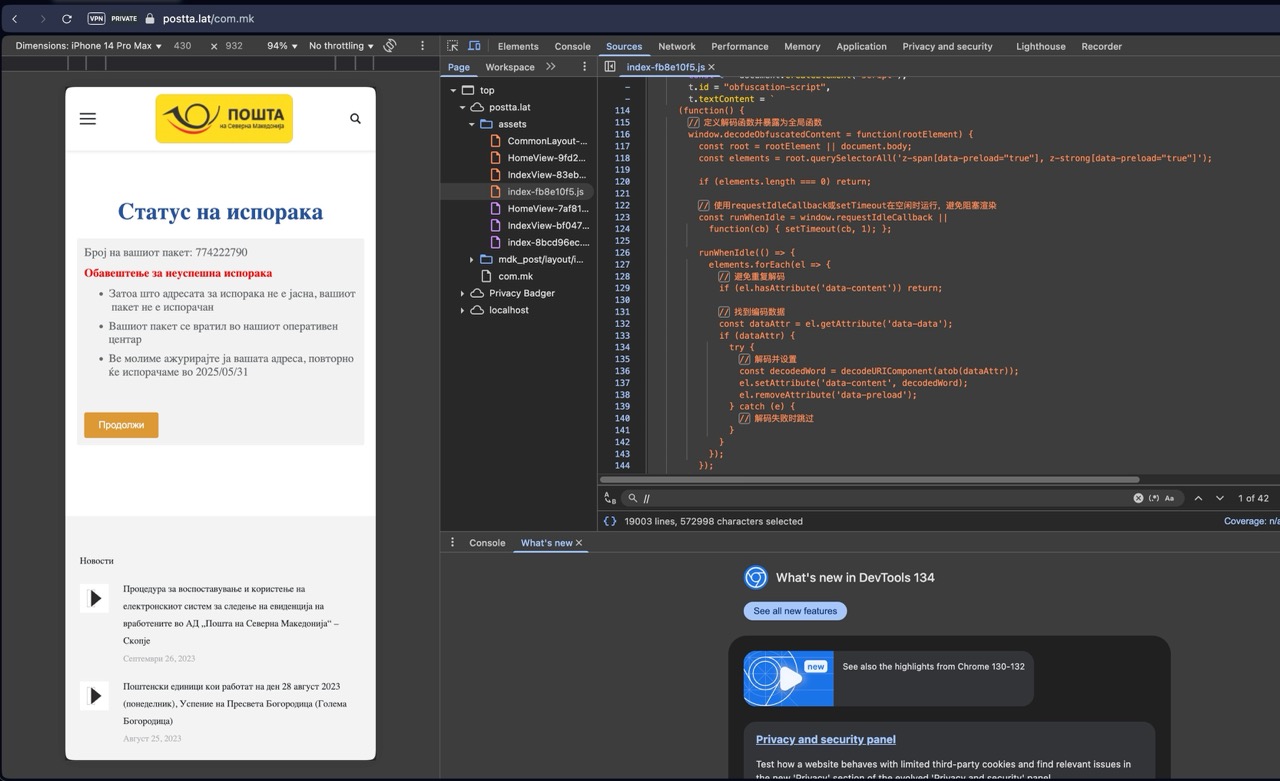
As of 29th of May, the scam continues with a new message format and new link postta.lat/com.mk, moved to new servers (see at the bottom). The software is exactly the same, we checked the comments in the source code.
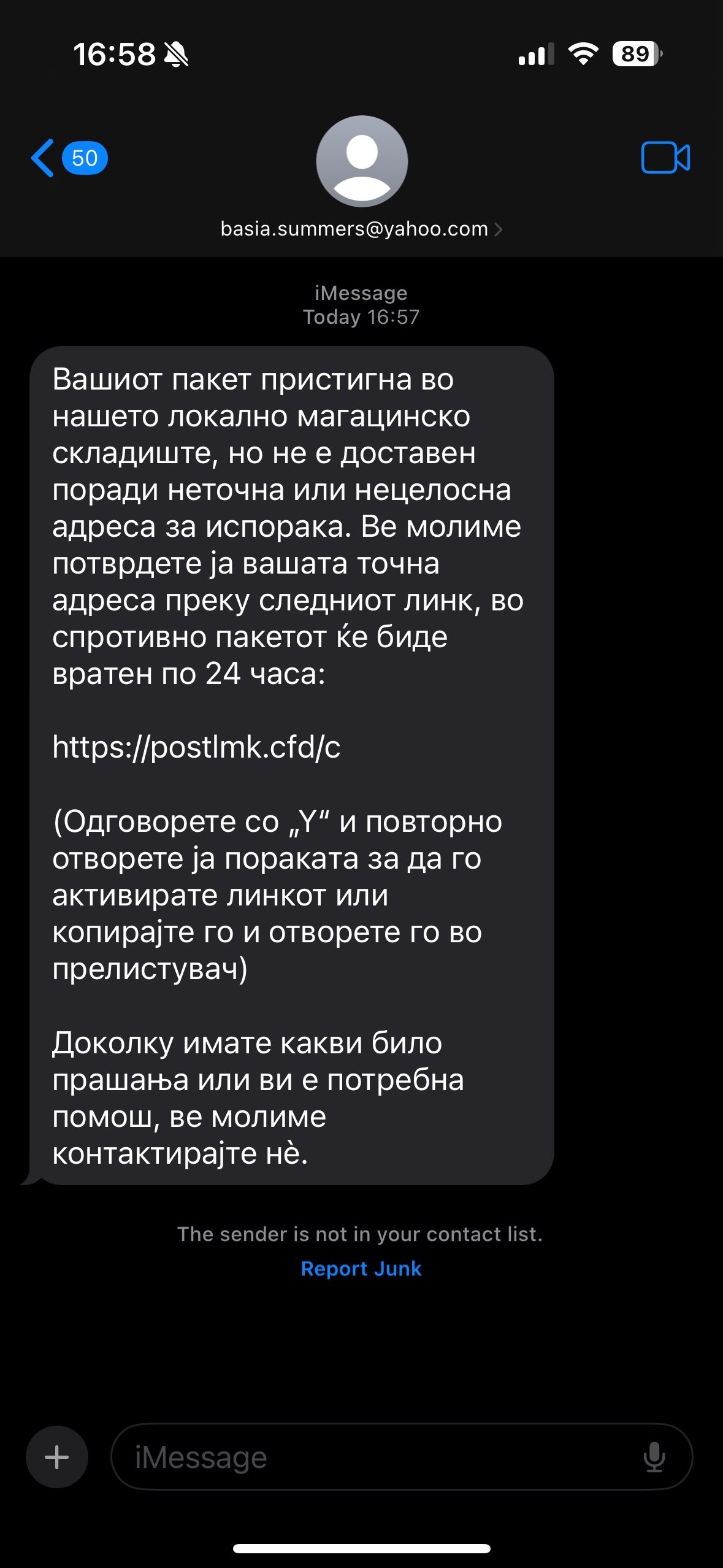
The scam uses SMS/iMessage delivery notifications to trick victims into providing personal information and credit card details. Victims receive a notification from an unknown sender that has nothing to do with Macedonian Post, claiming that a package has arrived at the local warehouse. Apparently the package cannot be delivered due to an incomplete address and will be returned within 24 hours if the issue is not resolved.
Another indicator is that the message contains "instructions" to enable the scam link by responding to the message or copy/paste the link elsewhere. This is a HUGE RED FLAG - someone EXPECTS that the link will be disabled, so it's very probably suspect.

The message aims to create a false sense of urgency to pressure victims into urgent action. The scam messages last acrosscarries links to at least two different domains, both registered on the 19th of May 2025.
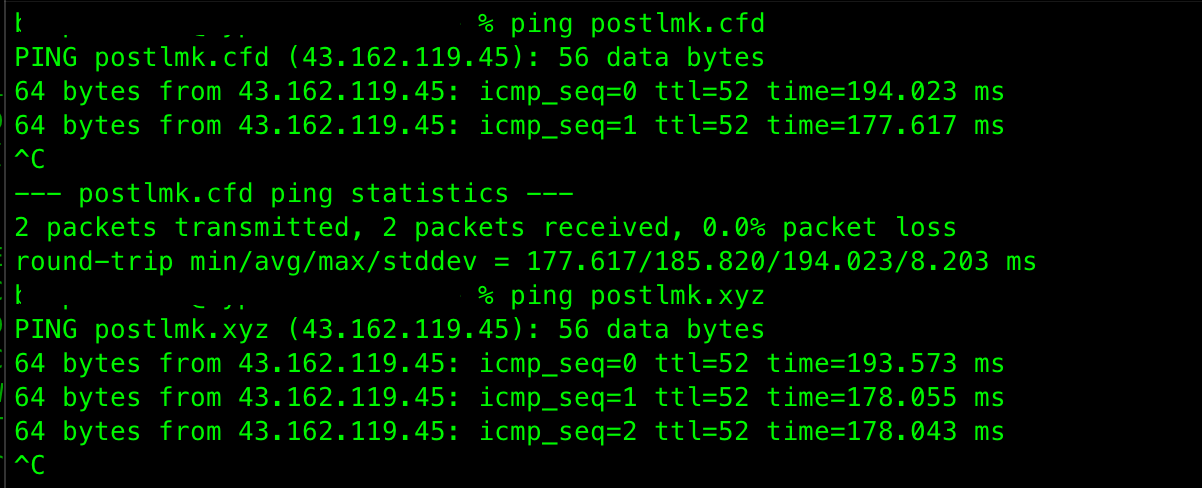
postlmk.cfdpostlmk.xyz
Update - as of 23rd of May 2025, the attackers are using another domain, and pushing the same campaign
postlmks.cfd
All the links resolve to the same IP address 43.162.119.45, registered to Tencent Cloud Computing - a Chinese company.
It's even shameful that they aren't even bothering to change the scam IP address.
Update - as of 29rd of May 2025, the attackers are using another domain, and pushing the same campaign with a new message
postta.lat/com.mk
Update - as of 4th of June 2025, the attackers are using another domain, and pushing the same campaign
plxxl.com
The content on the linked page impersonates the portal of Macedonian Post, but with some weird inconsistencies like the word for "Notification" - in Macedonian it's "Известување", but the text has a Serbian word "Обавештење".
Most of the hyperlinks don't work, others lead to the real website of Macedonian post. On the postlmk.xyz version of the site there are checks for opening the page from a computer - it doesn't render the page. It only renders the page if opened from a mobile phone.
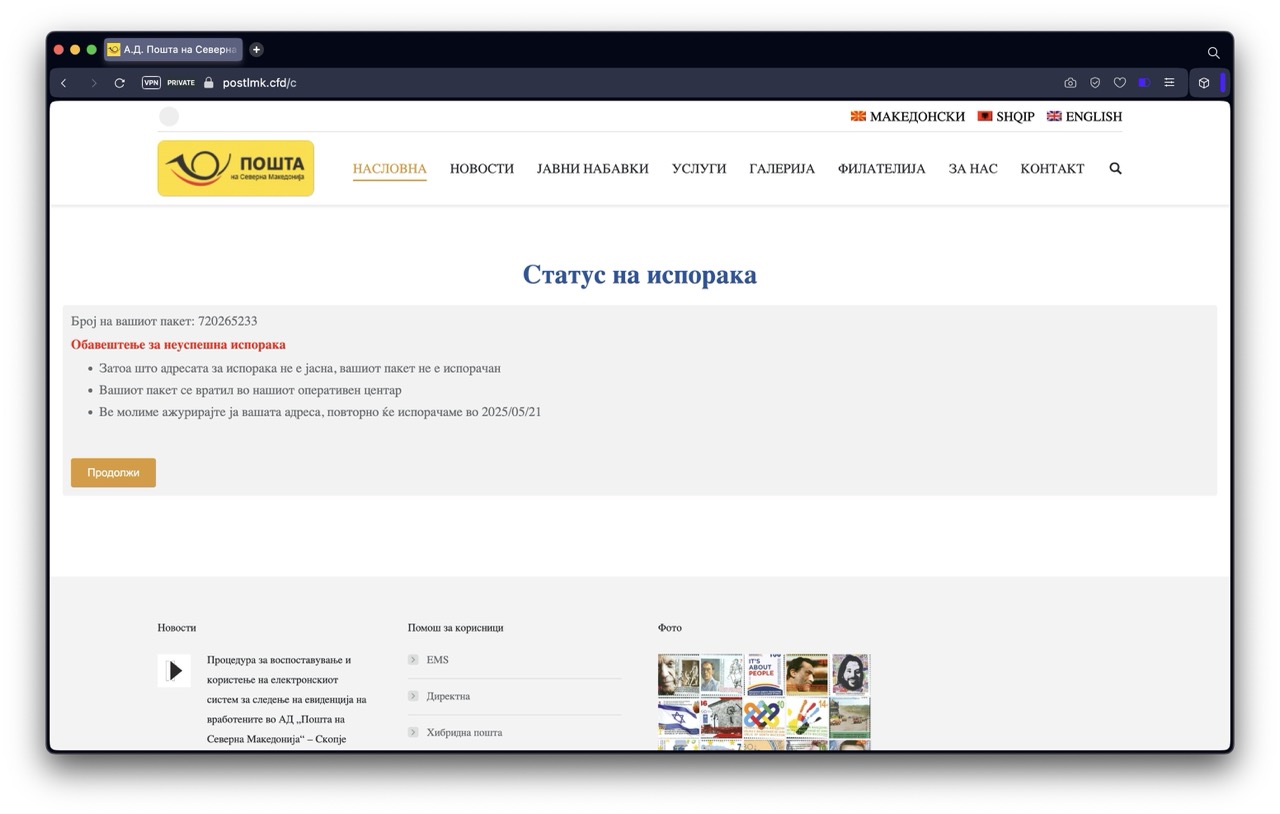
If the victim clicks to continue, there are two pages: first requests personal information (name, address, email, phone number) and the second one requests credit card details under the guise of "service fees" (22 denars).
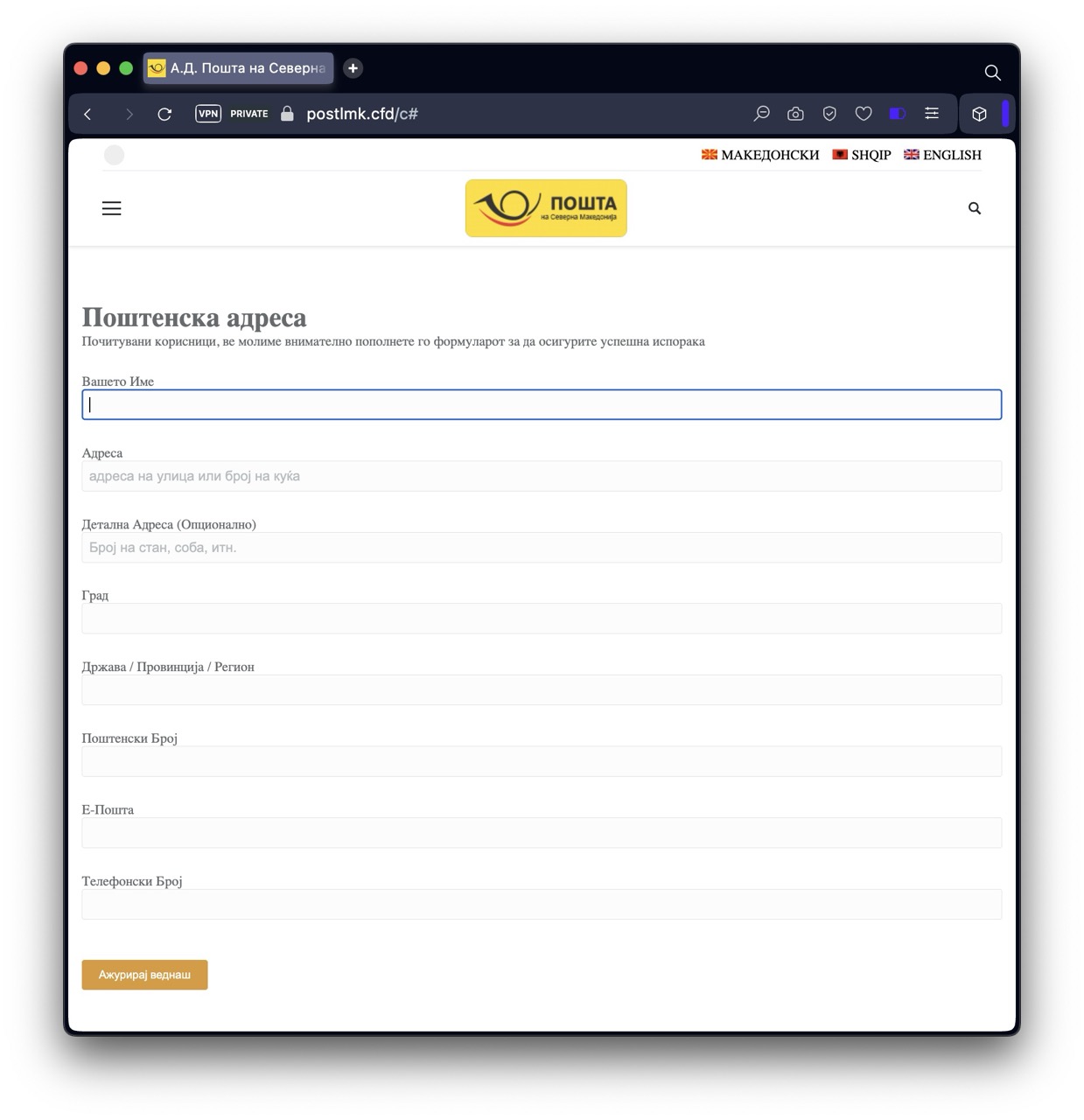
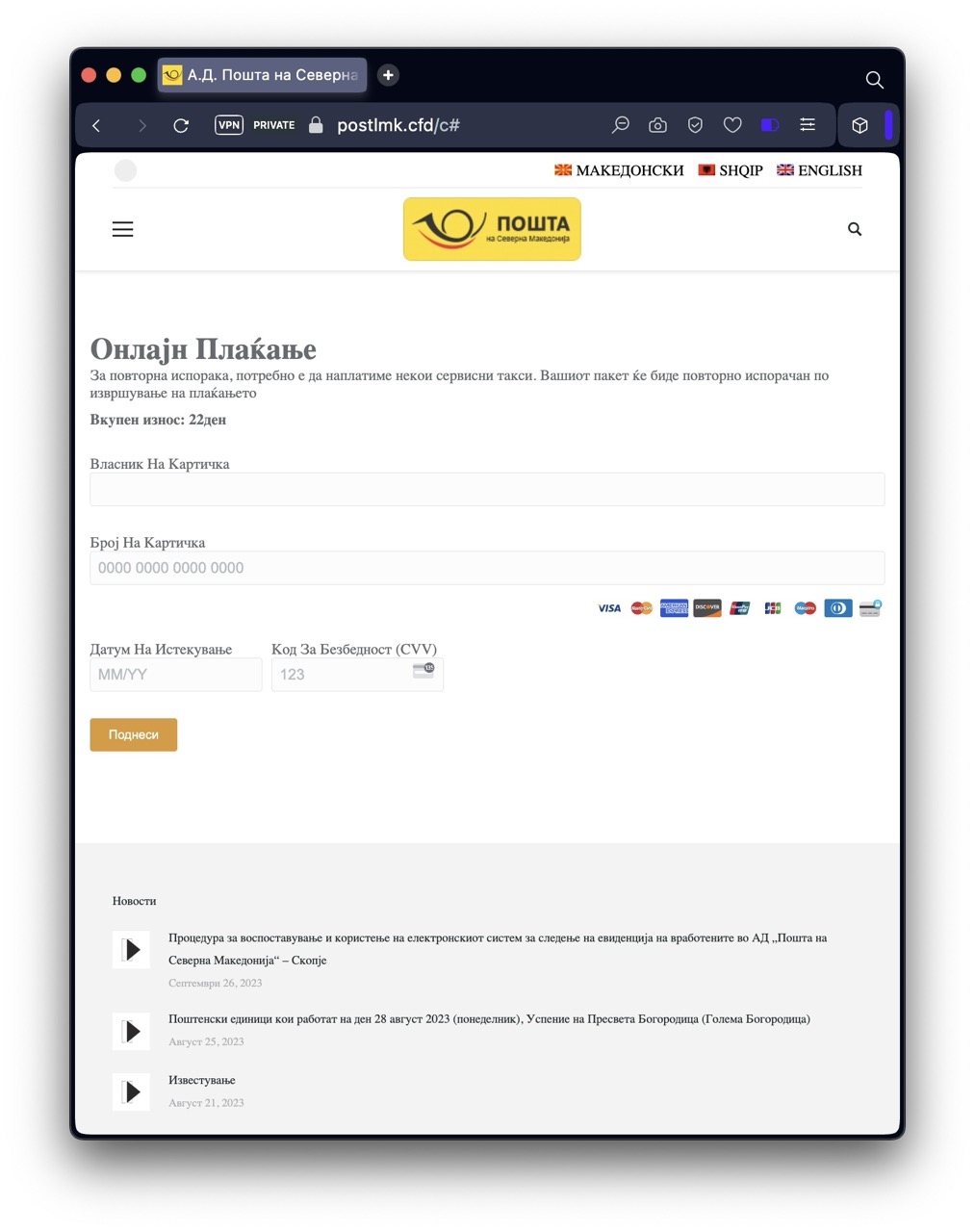
Both versions of the site have an active component that doesn't wait for the user to click submit to send the data to the server. Instead, they send each field as it's populated.
Even if the victim realizes that they are being scammed, some of the data will be stolen.
At the end of the process, the site tries to make a payment card transaction, but we don't have any information how much it tries to charge.
Analysis of the source code yielded chinese commments, which confirms that the campaign is at least partially architected by chinese speaking actors, and also shows part of the coding mechanism - to hide malicious code through "noise elements", strategically decode hidden content at optimal times, implement multiple detection avoidance techniques...
注册所有自定义元素= "Register all custom elements"注册噪声元素= "Register noise elements"定义解码函数并暴露为全局函数= "Define decoding function and expose it as a global function"使用requestIdleCallback或setTimeout在空闲时运行,避免阻塞渲染= "Use requestIdleCallback or setTimeout to run during idle time, avoiding blocking rendering"避免重复解码= "Avoid repeated decoding"找到编码数据= "Find encoded data"解码并设置= "Decode and set"解码失败时跳过= "Skip when decoding fails"页面加载完成后立即执行一次全局解码= "Execute global decoding once immediately after the page load completes"使用IntersectionObserver优化解码性能= "Use IntersectionObserver to optimize decoding performance"容器进入视口时解码其内容= "Decode content when container enters viewport"提前200像素开始解码= "Start decoding 200 pixels in advance"监听所有混淆容器= "Monitor all obfuscated containers"初始观察= "Initial observation"定期检查新容器= "Periodically check for new containers"降级方案:定期全局检查= "Fallback plan: periodic global checks"
The phishing site attempts to collect:
- Full name and complete address information
- Email address and phone number
- Complete credit card information including:
- Card number
- Expiration date
- CVV security code
How to stay safe
- DON'T RUSH - Be especially suspicious of messages creating urgency or threatening consequences
- Don't trust ANY unexpected mesages
- DON'T TRUST SHORTENED LINKS - They hide the real link, which is most probably fake and malicious
- Never click links or call numbers in unexpected messages
- Verify directly through official service websites (using a manually typed URL)
- Consult with someone else, a technical person.
- Check sender details carefully (official services don't use Yahoo email addresses)