Threat group Educated Manticore targets academia and cybersecurity experts
Take action: Whatever the attack motivation or the initial social engineering, all these attacks end up with an insistence for you to click on something and enter credentials. Be extremely suspicious of unexpected emails or messages, and verify independently - all or email the organization through official contact channel on the official site. NEVER click on links or call numbers in the unexpected message.
Learn More
Checkpoint reports that a threat group known as Educated Manticore, which is suspected to be supported by Iran has escalated cyber espionage activities targeting high-profile academics, journalists, and cybersecurity professionals with social engineering context of the ongoing Iran-Israel conflict.
Starting mid-June 2025, top cyber and computer science experts from leading Israeli universities became the primary targets of this campaign:
- The threat actors sent messages as fictitious employees of legitimate cybersecurity companies via email and WhatsApp communications. The objective is to extract credentials and bypass multi-factor authentication.
- The initial attack is carefully prepared and assisted by AI. The emails have a professional formal tone, structured layout, and error-free grammar. Some targets reported inconsistencies such as name mismatch between email body content and sender account names.
- In one instance, a WhatsApp message used the tensions between Iran and Israel to imply urgency, and the attackers even suggesting in-person meetings in Tel Aviv. This raised concerns about potential physical surveillance or physical attack on a person.
- In all cases, the initial message contains no malicious links, and attackers had a professional interaction with the target until they sent an online meeting link that lead to attacker-controlled phishing infrastructure.
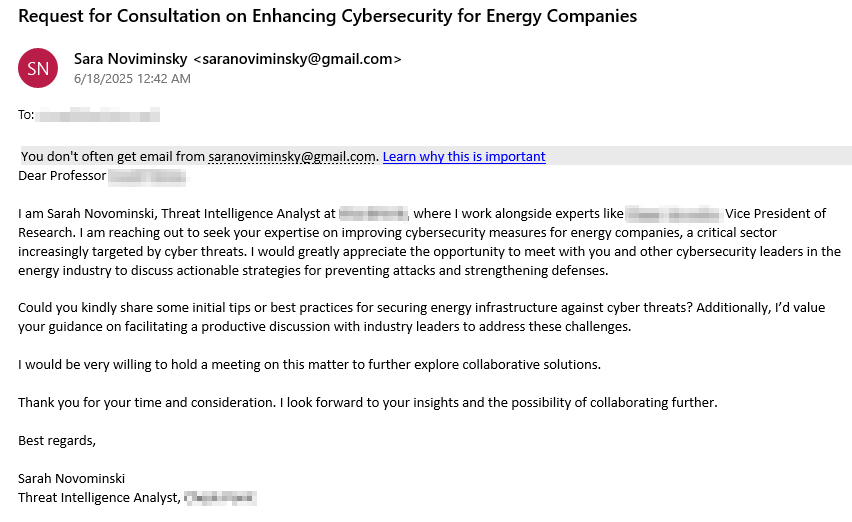
Initial email impersonating a fictitious Threat Intelligence Analyst. Source - CheckPoint research
The phishing infrastructure supports authentication flows to enable two-factor authentication relay attacks, where threat actors can complete multi-factor authentication against legitimate services using stolen data. The system handles various authentication mechanisms including email/username entry, SMS verification codes, password input, verification prompts, phone-based authentication, Google Authenticator integration, and security code entry.
A new and concerning aspect of the technical implementation is the incorporation of a passive keylogger that captures every keystroke and transmits the data in real-time through persistent WebSocket connections. This keylogger records every character typed, even if the user abandons the form or never submits it, providing attackers with comprehensive visibility into victim behavior and potential additional sensitive information.
The campaign used more than 130 unique domains along with numerous subdomains, using one or two domains for each targeted individual. From January 2025 onward, threat actors registered many domains used for targeted phishing operations, either hosting phishing kits or serving as backend infrastructure, with most domains registered through the NameCheap registrar.
The attackers were very aggressive in conversations, especially through WhatsApp, urging targets to click links with most attacks either succeeding or failing within one to two days before moving to the next target and discontinuing use of the same domain.
