Netflix payment phishing campaign stealing a lot of personal data
Take action: Be very suspicious of unexpected messages about failed subscriptions. Most are scams. Don't rush, a provider will not delete your data - if they do, they can't charge you for another year! Consult with technical people, NEVER click links or files in such emails or call numbers from the email. Manually navigate to the official website the email is claiming to be from and check your account status there.
Learn More
An active phishing campaign is targeting Netflix users via email that impersonates Netflix and attempts to steal personal, financial, and identity information. The attack is fairly standard in its delivery, but the theft approach is new: It doesn't try to charge the credit card immediately, focuses more on collecting a significant amount of personal information. We suspect that this is a data collection scam for resale.
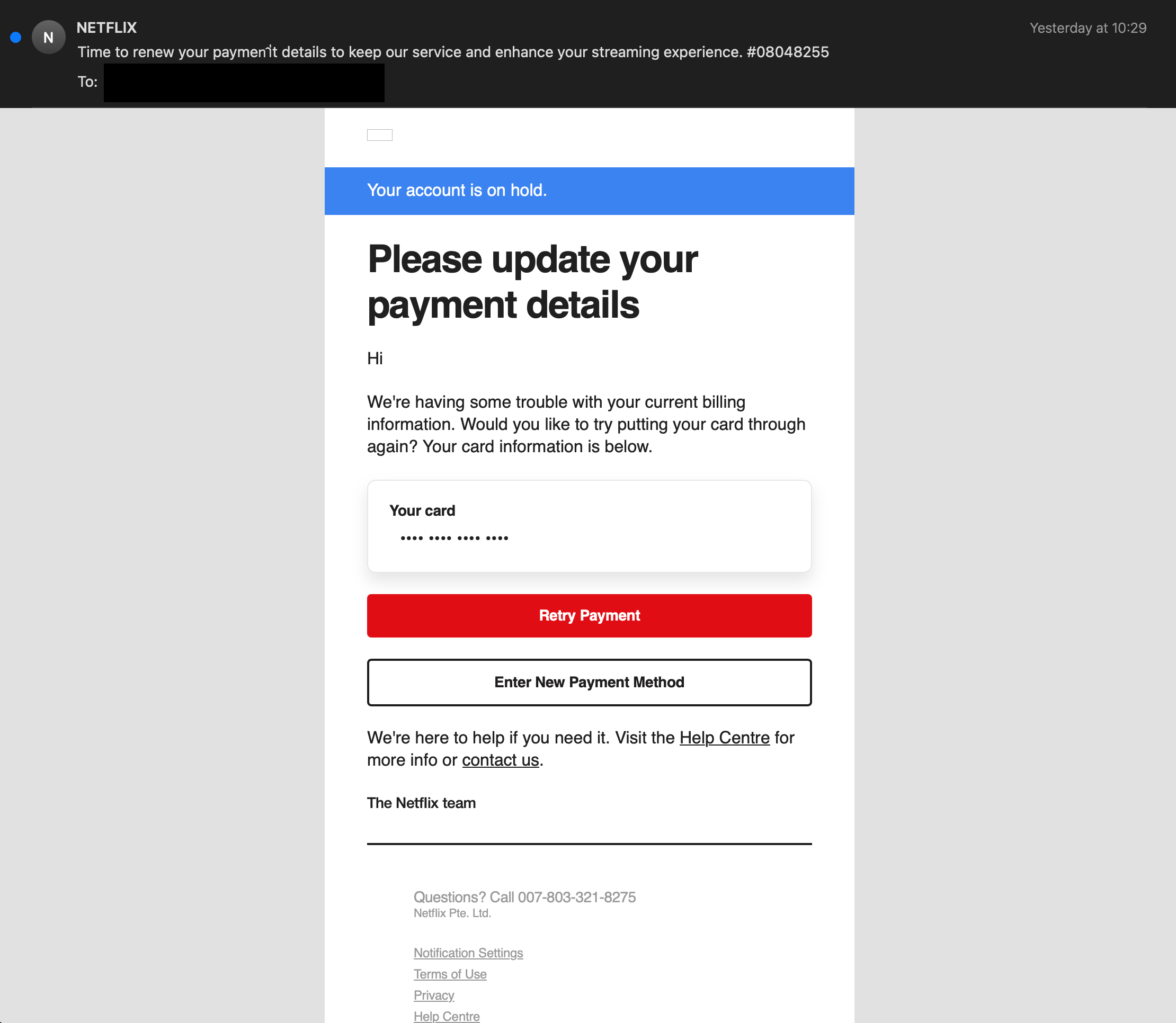
The attack begins with a HTML email that appears to be from Netflix with the subject line "Time to renew your payment details to keep our service and enhance your streaming experience." The attackers have used several well known techniques:
- Email Spoofing: The sender display name shows "NETFLlX" but the actual email address is "professional-service@telefonica.com" - completely unrelated to Netflix, and it's routed through open-relay server, not even related to the company Telefonica.
- Fake Urgency: Claims the user's account is "on hold" and payment information needs immediate updating
The email contains hidden characters and encoding tricks to bypass spam filters
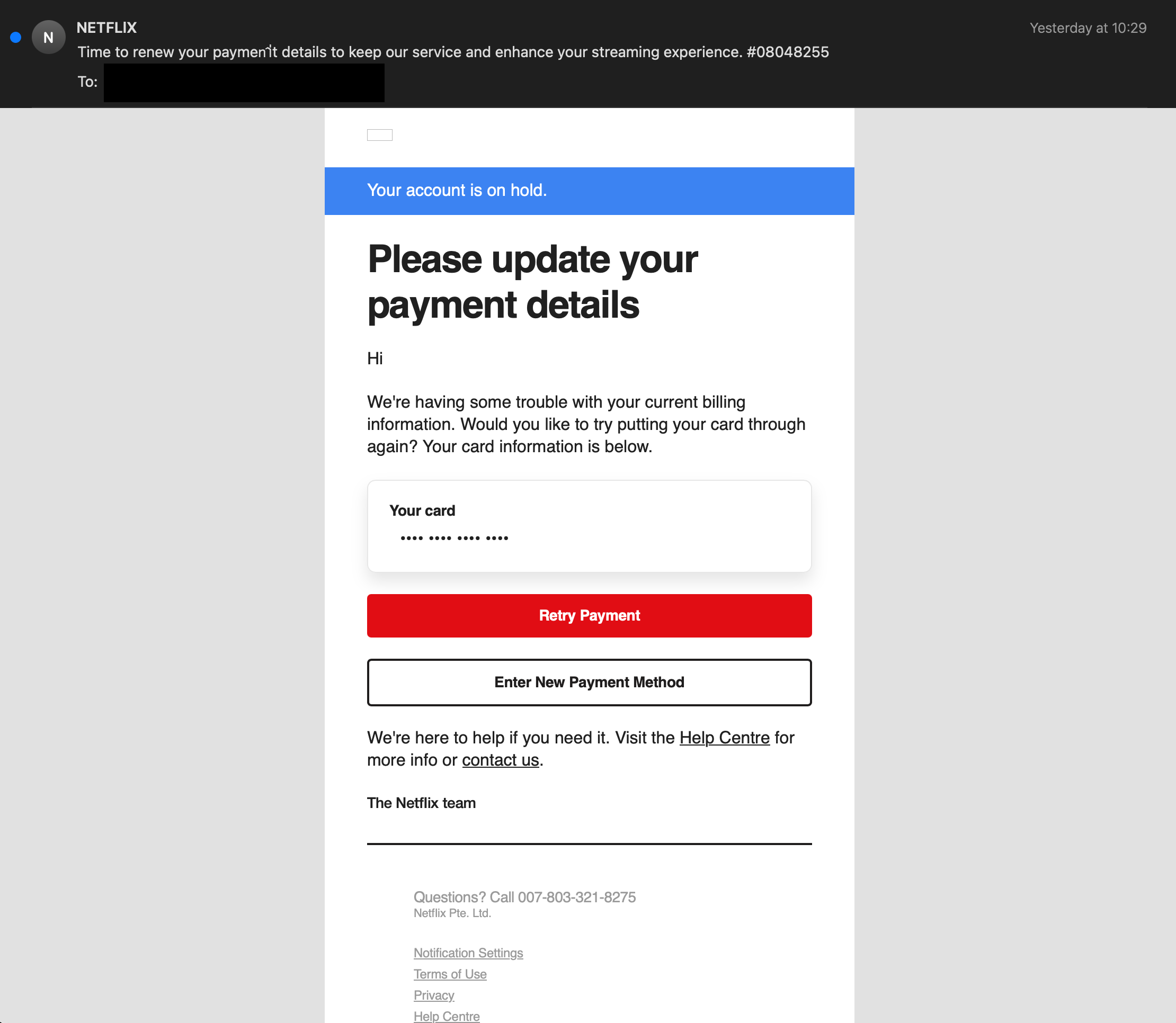
When victims click any button in the email, they're taken through a long redirect chain designed to stop any automatic scanners from identifying the link as a scam. This means that the link will bounce off multiple web servers, some of which are controlled by the criminals to be flexible in future redirects.
- Initial URL: Yahoo Mail's affiliate router is used as a trusted next link (owned by yahoo, but anyone can add a link)
(mobile.mail.yahoo.com/apps/affiliateRouter) - First redirect: Scribd's OAuth authorization endpoint with suspicious placeholder "YOUR_CLIENT_ID" - this is exploited as 'bounce' command to simply cause the Scribd servers to push the browser elsewhere
- URL Shortened site: A Korean URL shortener
(buly.kr), which hides the next URL - The unshortened url leads to a website with some scripts which continue the bouncing
(vvd.bz)onward - Another bounce server
(klarma.co)which responds with the final URL. We suspect this server is controlled by the hackers to reconfigure the final destination once the previous one is taken down. - that leads to the phishing site on
(sincodivdf.com.br)
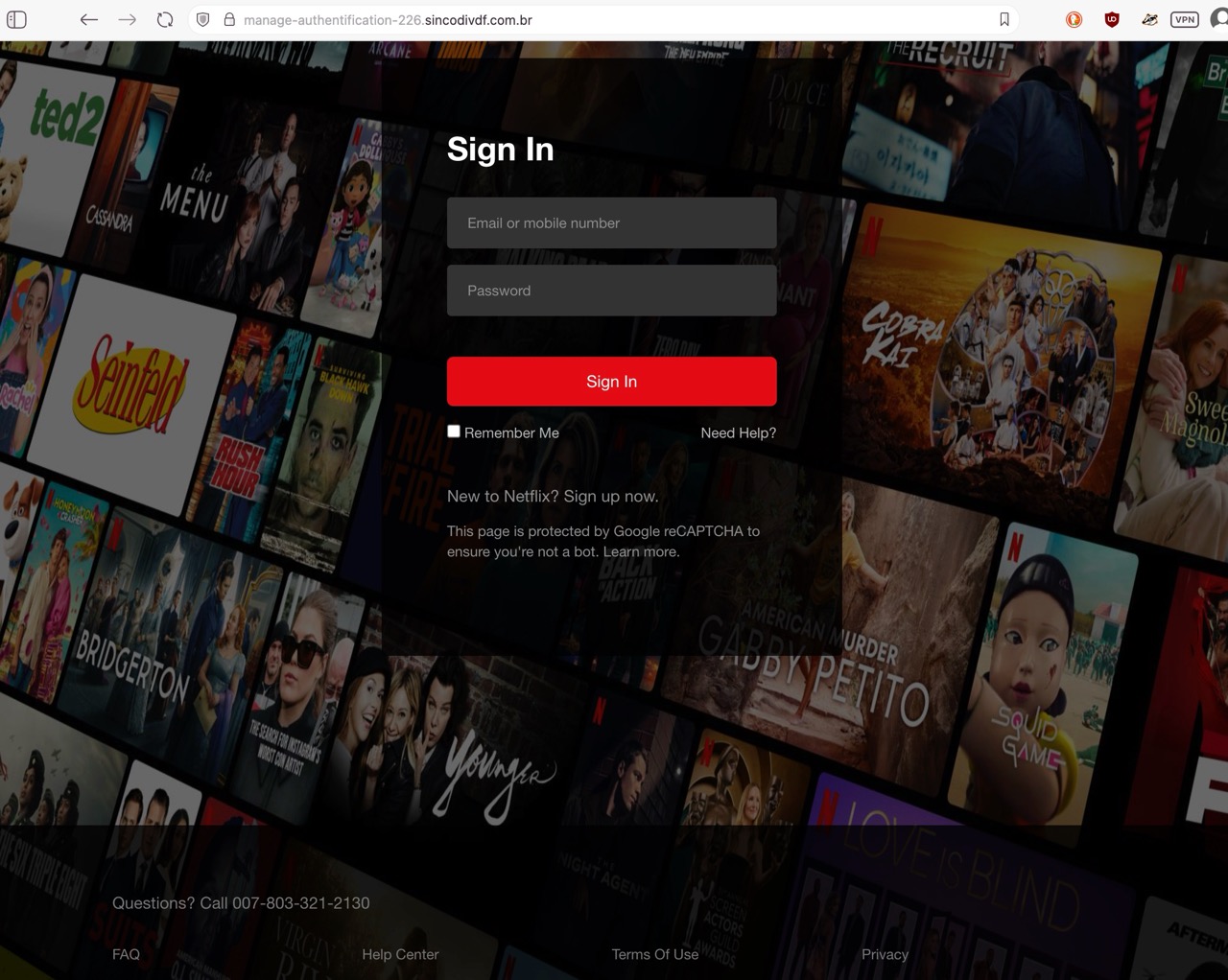
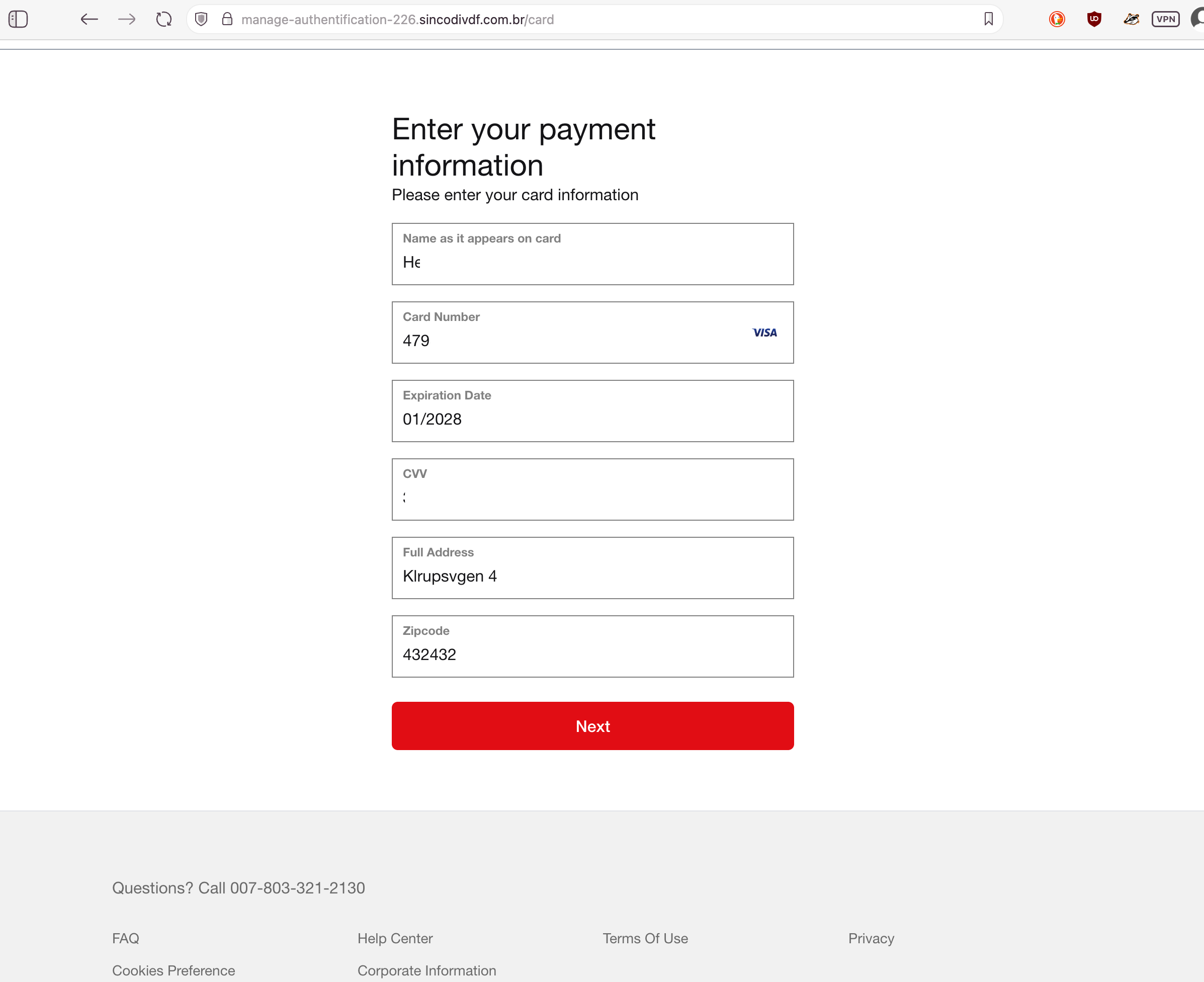
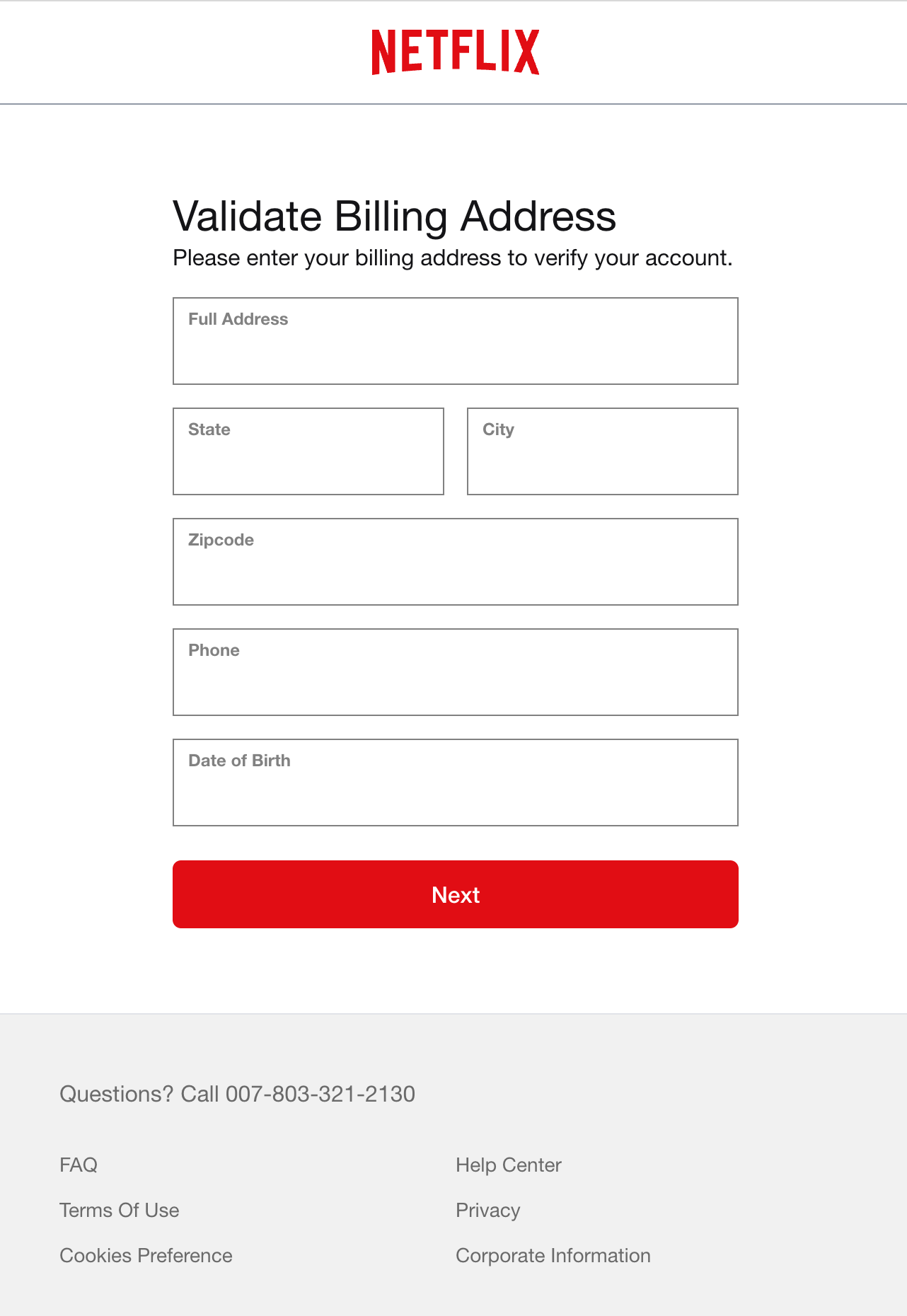
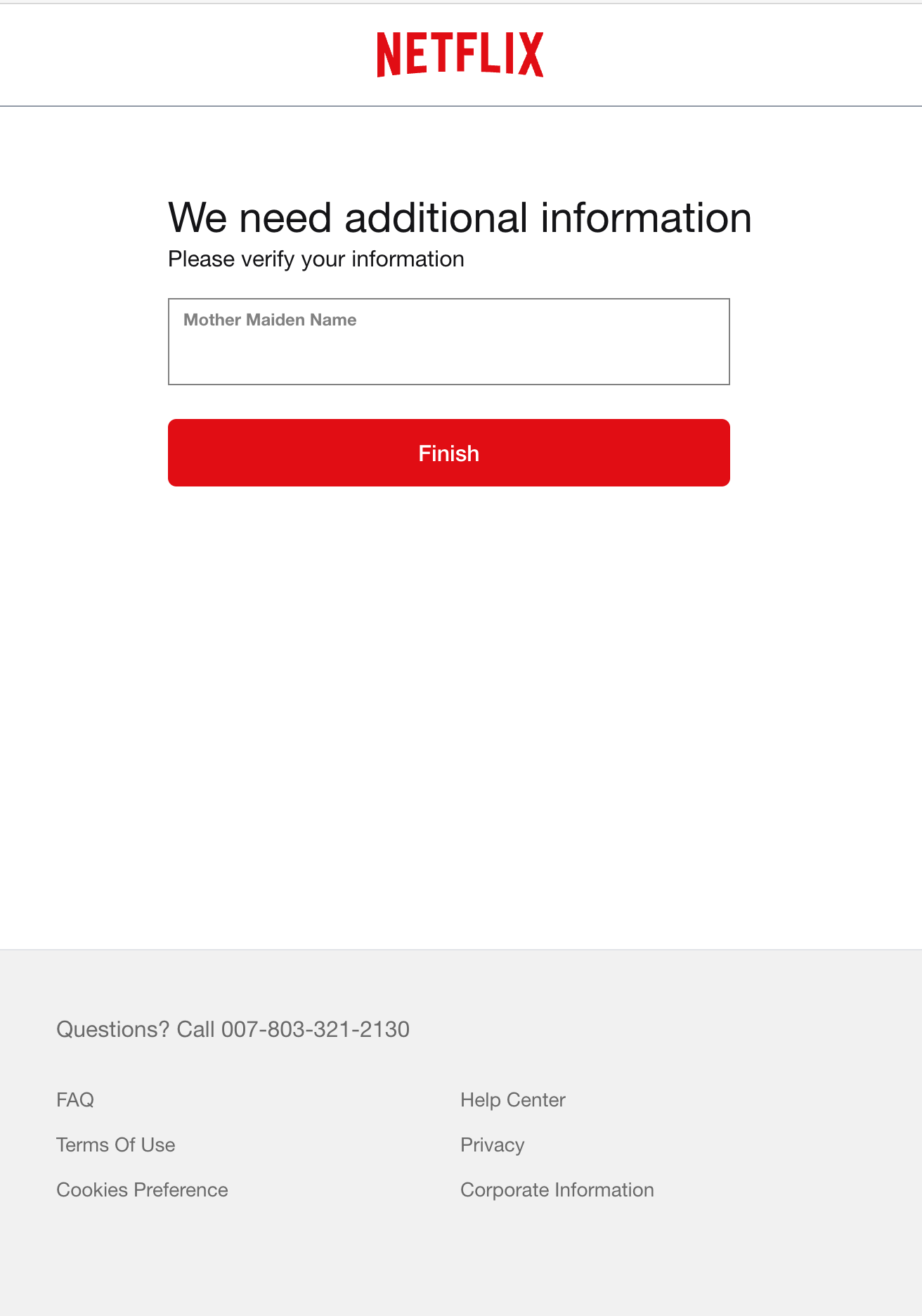
The phishing site mimics Netflix's design but collects extensive personal information across multiple pages:
- Email and password collection Page: Capturing the email and password of the victim
- Payment Information Page: Capturing complete credit card details including CVV
- Billing Address Verification: Collecting full address, phone number, and date of birth
- Account Verification Page: Requesting sensitive information like mother's maiden name
It must be noted that NONE of the data is immediately validated in a way that will tell the victim that something is happening. We suspect that any access or validation is done later or elsewhere.
Red Flags Identifying the Scam
- Suspicious Domain: The URL shows "manage-authentication-226.sincodivdf.com.br" instead of netflix.com
- Fictitious Support Number: Uses an obviously fake phone number "007-803-321-2130" (the 007 prefix is not a valid country code)
- Excessive Information Requests: Netflix would never request mother's maiden name and such extensive personal details
- Poor URL Structure: Legitimate companies don't use complex redirect chains through multiple services
If successful, this attack would give criminals:
- Ability to make unauthorized charges on the victim's credit card
- Personal information that could be used for identity theft
- Security verification details that could be used to compromise other accounts
- Contact information that could be used for future scams or sold to other criminals
How to stay safe
- Don't Rush! - Never fall for the urgency of the email. Take your time, read multiple times, think if this is expected.
- Don't click - Never click links in unexpected emails about account problems
- Log in Independently - Always access the claimed service directly through their official website or app, Never from the links in the email.
- If in doubt - consult with others