Cloud storage "payment failed" phishing attack
Take action: Unexpected "past deadline" payment requests are a very common phishing vector, since they imply urgency. Don't rush, a provider will not delete your data - if they do, they can't charge you for another year! Consult with technical people, NEVER click links or files in such emails. If you are concerned about your cloud storage account, manually navigate to the official website of your hosting by typing the URL directly in your browser and check your account status there.
Learn More
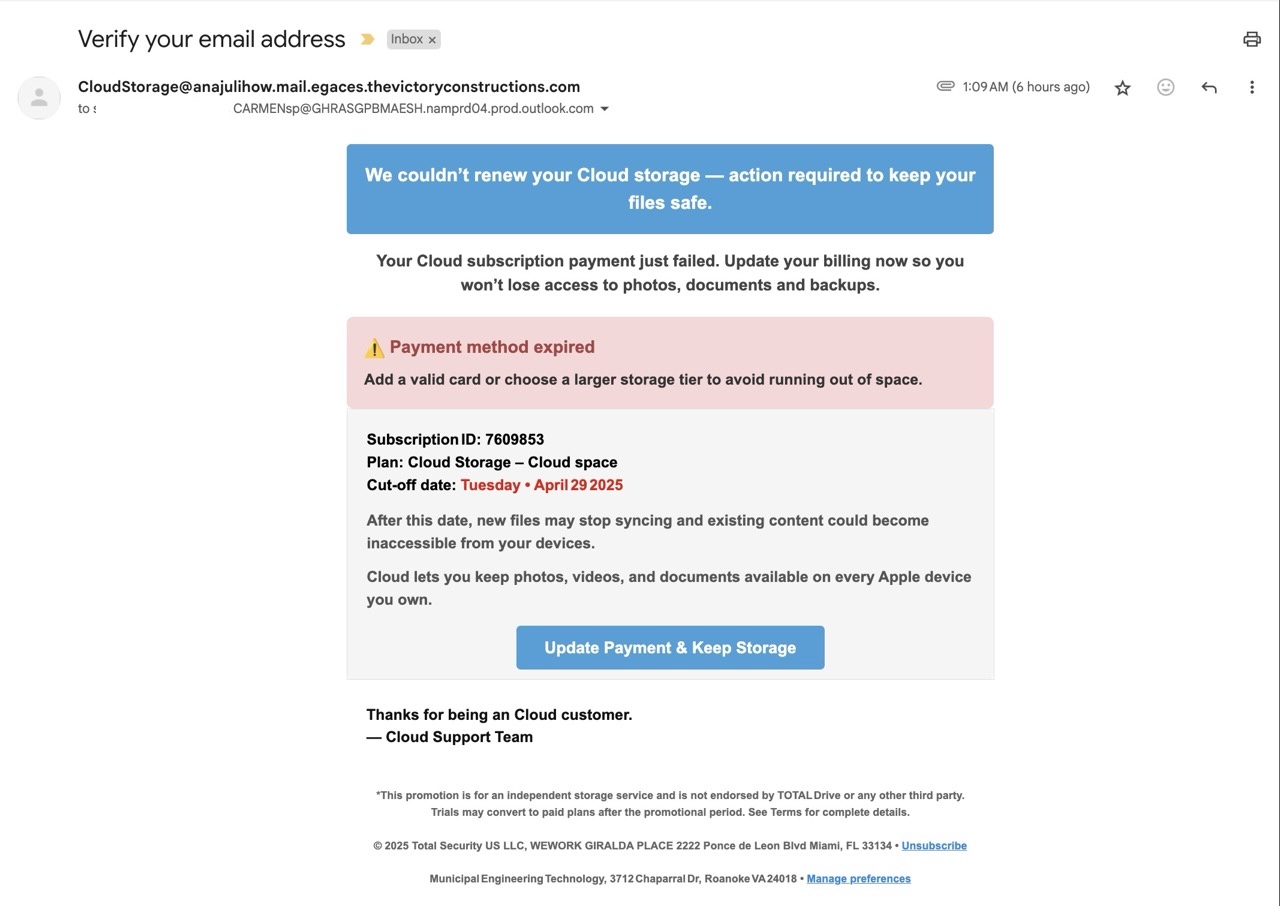
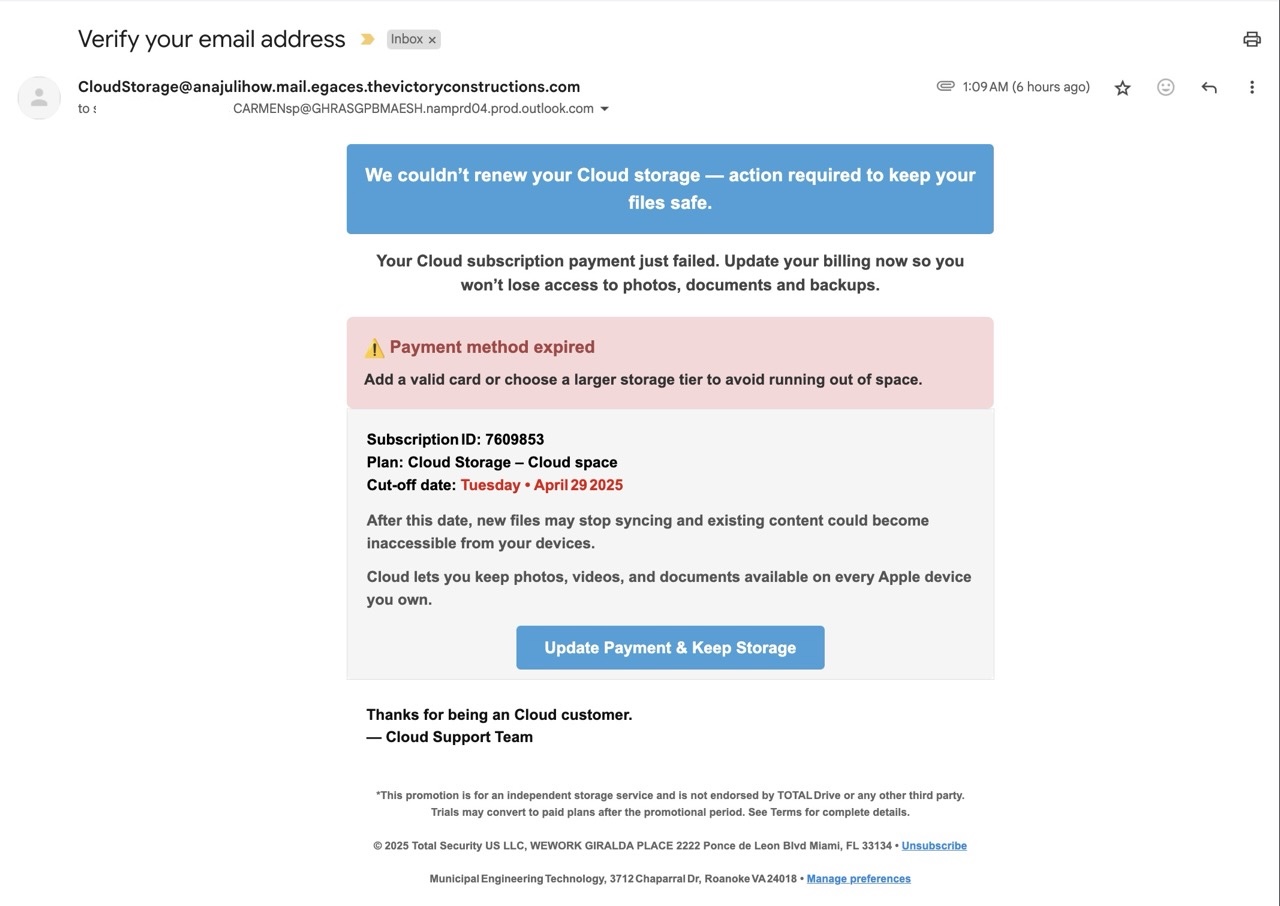
An active and very advanced phishing email is being actively sent to claim that a cloud storage service is alerting the recipient about a failed payment for their subscription. This is designed to create urgency by implying that access to their files will be lost unless payment information is updated.
It's designed to steal login credentials, payment information, and potentially install malware. The email uses multiple technical deception elements and psychological manipulation techniques to appear legitimate while hiding its malicious nature.
Unfortunately, the phishing page was not available or managed to evade our access attempts to access. The linked page has multiple redirects that pass through insecure websites, which causes most browsers to stop loading the pages. Forcing the visit resulted in a blank page - either it's geofenced to allow access only from some countries or requires very specific conditions to access - we got returned couldn't access it via browser or mobile with and without VPN.
The email renders as a message that a "cloud storage" subscription payment failed.
Initial Red Flags (just looking at the email)
- The sender claims to be "CloudStorage" but is sent from email:
CloudStorage@anajulihow.mail.egaces.thevictoryconstructions.com. This is a blatant mismatch - legitimate cloud services use their own domains (e.g., apple.com, microsoft.com, google.com) - No branding or naming of which "CloudStorage" the email is represented.
- The email references generic or vague product names - "Cloud" and "Total Drive", which look like cloud storage but are not specifically a product, just a vague hint.
- The email contains multiple CC addresses with nonsensical domain names - nobody sends subscription payment failed to multiple people at the same time.
- The email footer contains addresses from multiple unrelated businesses:
- "Total Security US LLC, WEWORK GIRALDA PLACE 2222 Ponce de Leon Blvd Miami, FL 33134"
- "Municipal Engineering Technology, 3712 Chaparral Dr, Roanoke VA 24018"
Email deep analysis
The email has a lot of built-in instruments to bypass antispam and antiphishing filters:
- The body contains large blocks of gibberish text to force skipping of antispam analysis - (e.g., "eiehdzukaoigfyzp...") repeated hundreds of times. That gibberish text has no function in the email, is not rendered but dramatically increases the size of the email, which is one way to bypass antispam filters since large emails are typically skipped by antispam and scanned with an antivirus assuming an attachment.
...
eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgghfzqxrtl=
fetufnzuxqcophfsasuouekrsqp eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojr=
dtmsgfjcebklnfustqgghfzqxrtlfetufnzuxqcophfsasuouekrsqp eiehdzukaoigfyzpxer=
endzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgghfzqxrtlfetufnzuxqcophfsasu=
ouekrsqp eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqg=
ghfzqxrtlfetufnzuxqcophfsasuouekrsqp eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrw=
pjkrqtojrdtmsgfjcebklnfustqgghfzqxrtlfetufnzuxqcophfsasuouekrsqp eiehdzukao=
igfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgghfzqxrtlfetufnzuxq=
cophfsasuouekrsqp eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjceb=
klnfustqgghfzqxrtlfetufnzuxqcophfsasuouekrsqp eiehdzukaoigfyzpxerendzhrfmcf=
hvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgghfzqxrtlfetufnzuxqcophfsasuouekrsqp e=
iehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgghfzqxrtlf=
etufnzuxqcophfsasuouekrsqp eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrd=
tmsgfjcebklnfustqgghfzqxrtlfetufnzuxqcophfsasuouekrsqp eiehdzukaoigfyzpxere=
ndzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgghfzqxrtlfetufnzuxqcophfsasuo=
uekrsqp eiehdzukaoigfyzpxerendzhrfmcfhvvuyudrwpjkrqtojrdtmsgfjcebklnfustqgg=
hfzqxrtlfetufnzuxqcophfsasuouekrsqp=20
...
- Duplicate content to confuse antispam/antiphishing - Contains two different HTML templates: one for "Cloud Storage" and another for "AL.com" verification. Only the first one is rendered. The second is there just to reduce spam/phishing indicators.
- Links to Microsoft hosted pages to increase trust - All links lead to a Windows Blob storage to indicate trust of the link - The links lead to
https://j88h6hsknsivez64.blob.core.windows.net/...which is a user managed storage where HTML files can be published to further redirect the target. Antispam/antiphishing filters will see a Microsoft Azure linkwindows.net/.and flag the links as safe. - Additional noise in the email body - Over 100 random email addresses with format:
[random string]@WCHVJRNDTE.info.eduThis padding helps bypass spam filters by obscuring the malicious content and manipulating spam-detection algorithms
...
mNHWWjNGKpJ7fUvvTLucJs2weuK7T4e8CoAa2QQgYfnsygvZEl4Adl7nbHf2EJZTSFODrSz45yC=
s@WCHVJRNDTE.info.edu
sdZmgc67u7vlCD7tirqBL9b6wJIiISZqmqzgHcWtLE4A3BTGkSzZq82cnsmknV9mNYi2DUJ6eSR=
3@WCHVJRNDTE.info.edu
FGaWGCg0xBCsSJuuP15R6Pl9XOn0t6s2wFgH1RCJQ8gQ4pTzDAOS48IGZ5ApyQOH9jzWfgmmJtX=
B@WCHVJRNDTE.info.edu
t5tBvp2K6C0443wJ5lPe2E88XcLSp4LIHlOmz1b4fQ2KTTyJ0AvRDzS7PZAT45szX1u6DGzSVyM=
e@WCHVJRNDTE.info.edu
...
- Fake routing injected in header - The email header contains intentionally injected fake message routing through legitimate services like Salesforce, Schwab, and Steam:
Received: from smtp-0e2a808594441e080.core1.sfdc-yfeipo.mta.salesforce.com (smtp-0e2a808594441e080.core1.sfdc-yfeipo.mta.salesforce.com. )
by mx.google.com with ESMTPS id af79cd13be357-7b67887ce00si302213785a.518.2024.11.27.02.42.06
for <giveme.justinbox@gmail.com>
(version=TLS1_3 cipher=TLS_AES_256_GCM_SHA384 bits=256/256);
Wed, 27 Nov 2024 02:42:07 -0800 (PST)
Received: from mta2.mail.schwab.com (mta2.mail.schwab.com. )
by mx.google.com with ESMTPS id af79cd13be357-7b66f23bf10si632228485a.288.2024.11.27.02.29.07
for <giveme.justinbox@gmail.com>
(version=TLS1_2 cipher=ECDHE-ECDSA-AES128-GCM-SHA256 bits=128/128);
Wed, 27 Nov 2024 02:29:07 -0800 (PST)
Received: from smtp-01-tuk1.steampowered.com (smtp-01-tuk1.steampowered.com. )
by mx.google.com with ESMTPS id d9443c01a7336-214f8787c1esi26915675ad.491.2024.11.27.02.23.05
for <giveme.justinbox@gmail.com>
(version=TLS1_3 cipher=TLS_AES_256_GCM_SHA384 bits=256/256);
Wed, 27 Nov 2024 02:23:05 -0800 (PST)
While we were unable to open the final scam page, but this phishing attack usually aims to steal
- Cloud storage login credentials
- Credit card information (under the guise of "updating payment method")
- Potentially install malware (the link could lead to a malicious download)
How to stay safe?
- DON'T RUSH - Think about the unexpected email. Ask yourself, why am I receiving this? Report unexpected suspicious emails to your security team or consult with a technical person.
- Nothing is this urgent! - Be suspicious of urgent financial requests or threats about losing access to services
- Trust Nothing Unexpected - Treat all unexpected messages as suspicious. Never
- Don't trust links or files - Do not click links or open files in unexpected emails, even if they appear legitimate
- Sender name can be faked - Always check the sender email address, not the displayed name in the email
- Verify independently - Verify the information information directly via known, legitimate channels (not via any phone or link in the unexpected emails)